Leader of Qakbot cybercrime network indicted in U.S. crackdown
Security Affairs
MAY 24, 2025
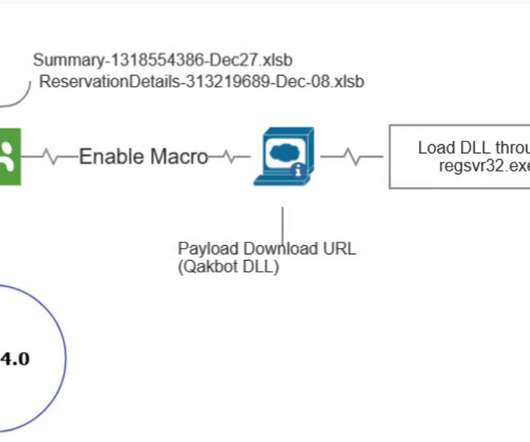
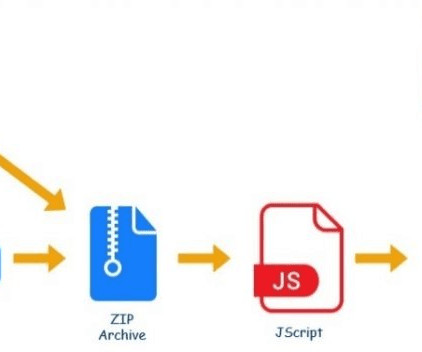
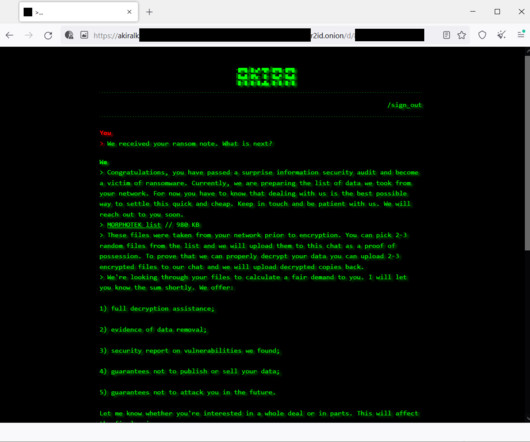
Qakbot , also known as QBot, QuackBot and Pinkslipbot, is an info-stealing malware that has been active since 2008. The malware spreads via malspam campaigns, it inserts replies in active email threads. Gallyamov began developing Qakbot in 2008, building a team that expanded its capabilities over the time. and abroad.




































Let's personalize your content