Who’s Behind the GandCrab Ransomware?
Krebs on Security
JULY 8, 2019
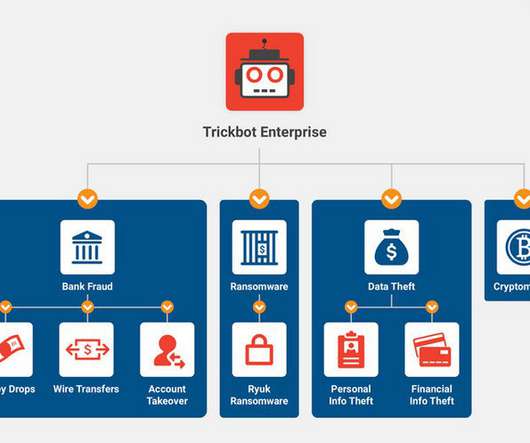
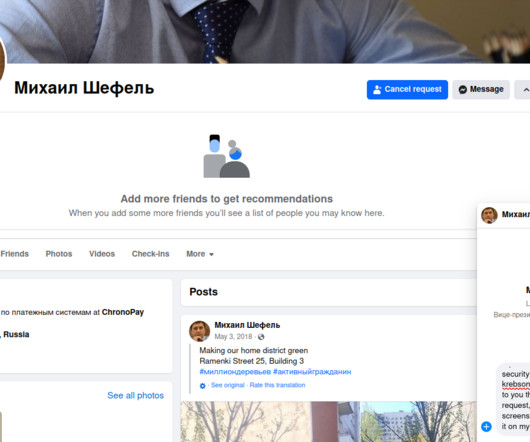
The crooks behind an affiliate program that paid cybercriminals to install the destructive and wildly successful GandCrab ransomware strain announced on May 31, 2019 they were terminating the program after allegedly having earned more than $2 billion in extortion payouts from victims. Image: Malwarebytes. The GandCrab identity on Exploit[.]in








































Let's personalize your content