Giving a Face to the Malware Proxy Service ‘Faceless’
Krebs on Security
APRIL 18, 2023
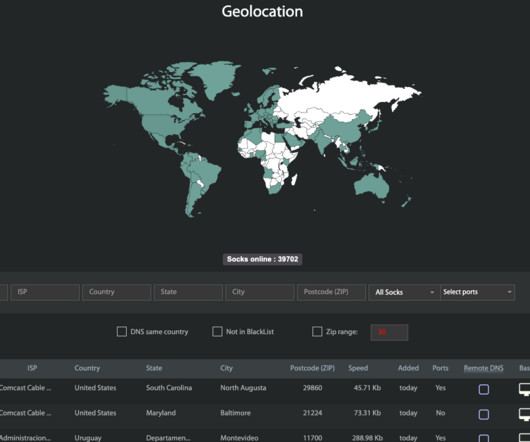
Kilmer said Faceless has emerged as one of the underground’s most reliable malware-based proxy services, mainly because its proxy network has traditionally included a great many compromised “Internet of Things” devices — such as media sharing servers — that are seldom included on malware or spam block lists.

























Let's personalize your content