Beware Ukraine-themed fundraising scams
Malwarebytes
APRIL 6, 2022
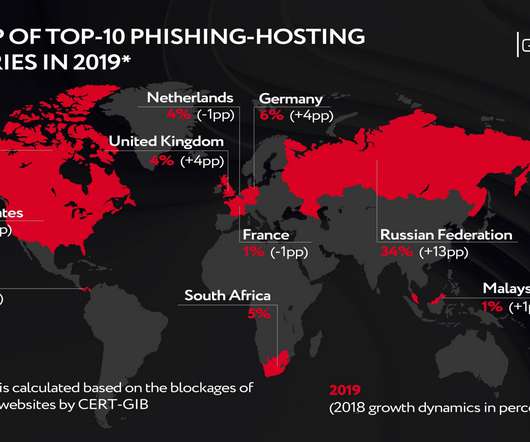
It was rife during the earthquake and tsunami of 2011 , with bogus Red Cross websites and email addresses set up to part people from their money. Reports indicate a big run on phishing and scams. The tactics used match those deployed in 2011, and pretty much every other major catastrophe. Cryptocurrency scamming is rampant.















Let's personalize your content