Six Charged in Mass Takedown of DDoS-for-Hire Sites
Krebs on Security
DECEMBER 14, 2022
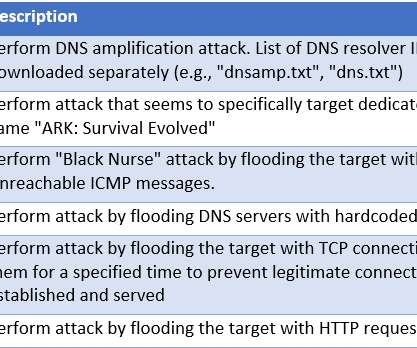
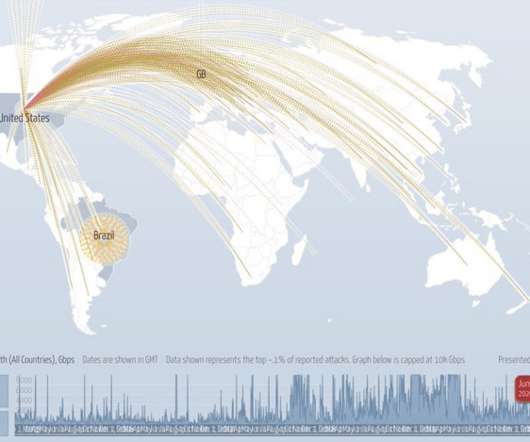
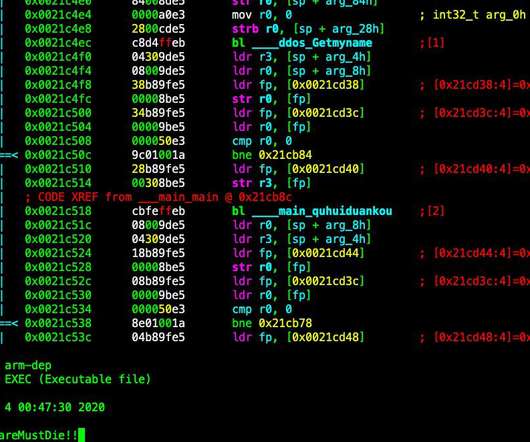
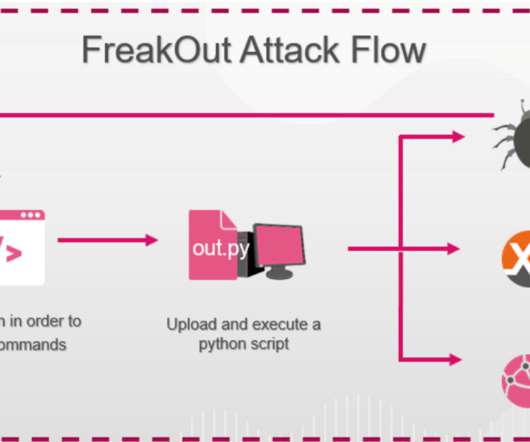
Department of Justice (DOJ) today seized four-dozen domains that sold “booter” or “stresser” services — businesses that make it easy and cheap for even non-technical users to launch powerful Distributed Denial of Service (DDoS) attacks designed knock targets offline. The DOJ also charged six U.S.
































Let's personalize your content