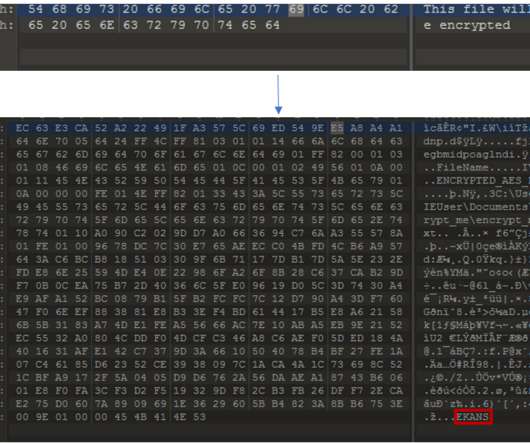
BrandPost: Detect Malware in Encrypted Traffic for Improved Security Visibility
CSO Magazine
OCTOBER 11, 2021
According to the Ponemon Institute's 2021 Global Encryption Trends Study, 50% of organizations have an encryption plan consistently applied across their entire environment—up from around 40% in 2015, and 25% in 2010.
































Let's personalize your content