U.S. Charges 4 Chinese Military Officers in 2017 Equifax Hack
Krebs on Security
FEBRUARY 10, 2020
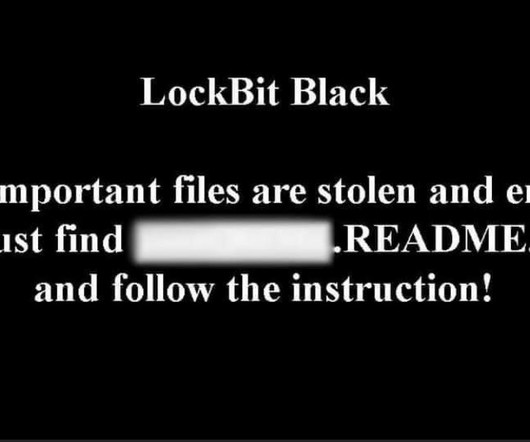
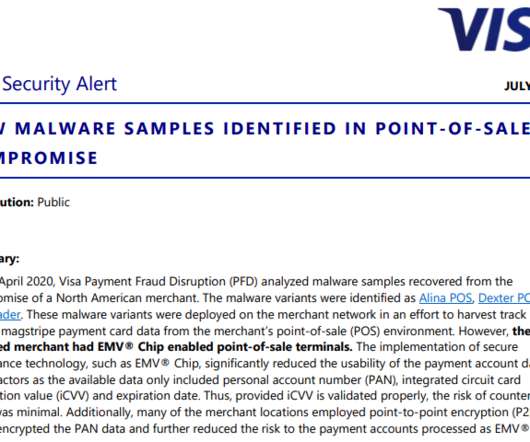
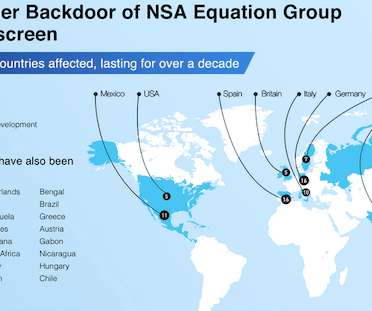
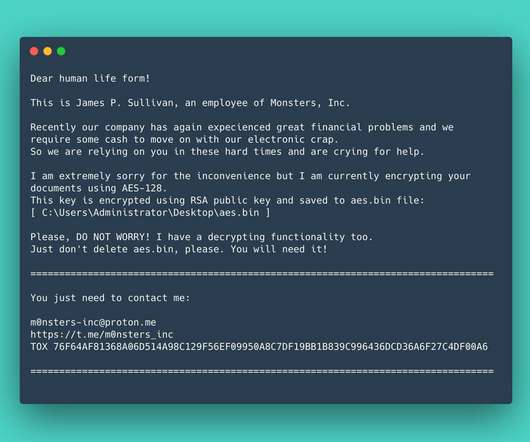
Justice Department today unsealed indictments against four Chinese officers of the People’s Liberation Army (PLA) accused of perpetrating the 2017 hack against consumer credit bureau Equifax that led to the theft of personal data on nearly 150 million Americans. dubbed the “China Initiative Conference.”






































Let's personalize your content