SHARED INTEL: How ransomware evolved from consumer trickery to deep enterprise hacks
The Last Watchdog
JUNE 21, 2020
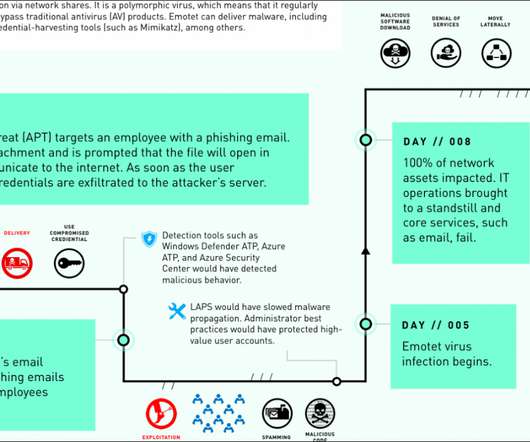
The above-mentioned AIDS Trojan hailing from the distant pre-Internet era was the progenitor of the trend, but its real-world impact was close to zero. RaaS rollout 2015 – 2018. The GandCrab RaaS that appeared in early 2018 was one of the last high-profile threats targeting individuals on a large scale.



































Let's personalize your content