Feds Charge Five Men in ‘Scattered Spider’ Roundup
Krebs on Security
NOVEMBER 21, 2024
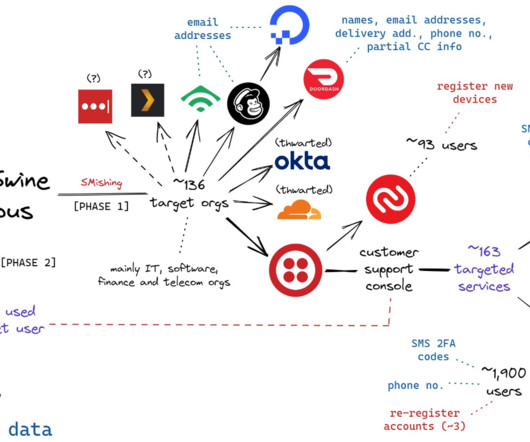
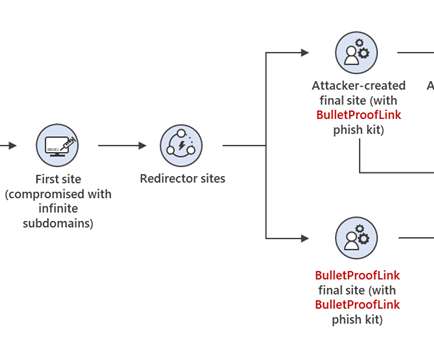
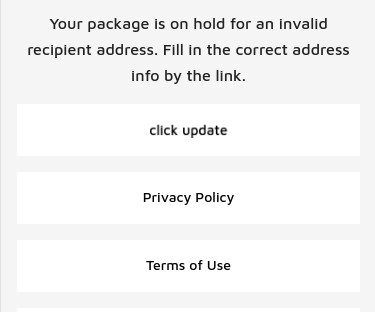
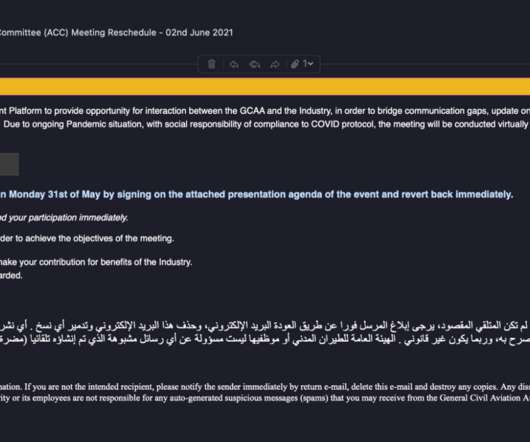
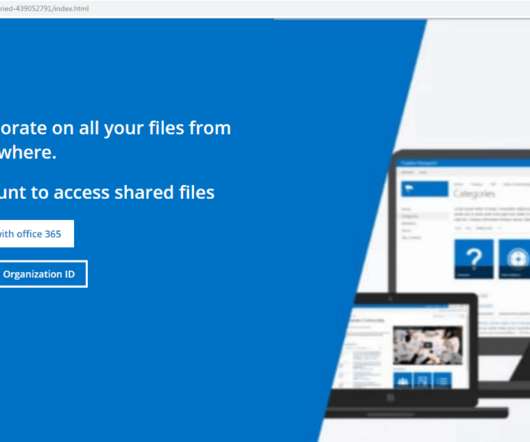
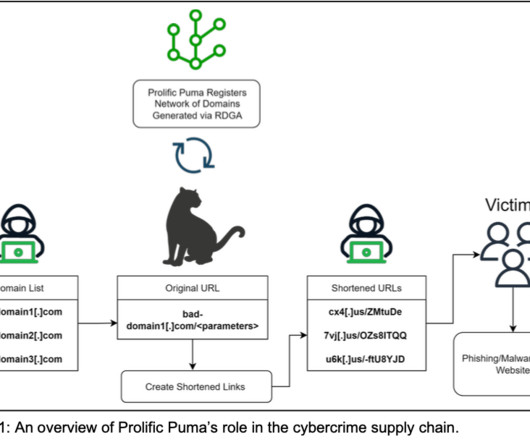
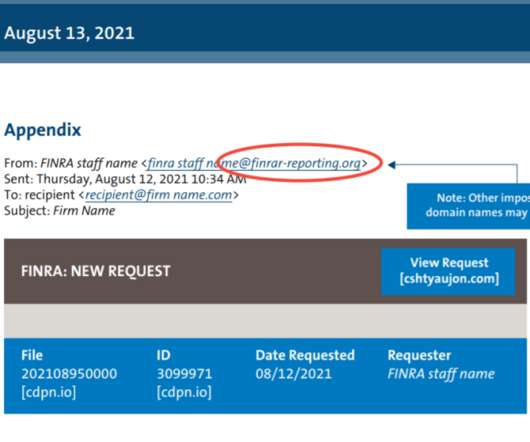
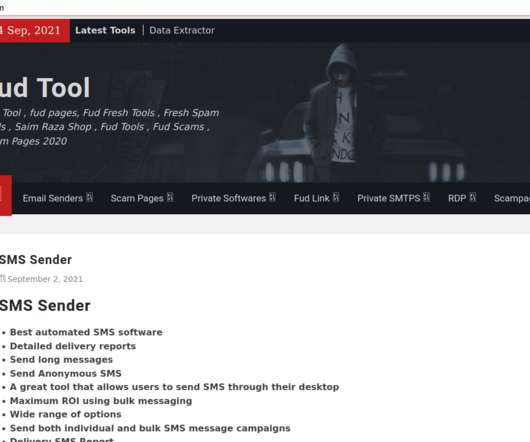
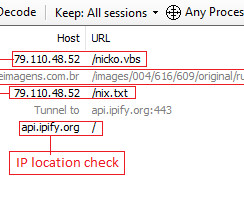
A visual depiction of the attacks by the SMS phishing group known as Scattered Spider, and Oktapus. Some SMS phishing messages told employees their VPN credentials were expiring and needed to be changed; other phishing messages advised employees about changes to their upcoming work schedule. com and ouryahoo-okta[.]com.
































Let's personalize your content