SEC X account hacked to hawk crypto-scams
Malwarebytes
JANUARY 10, 2024
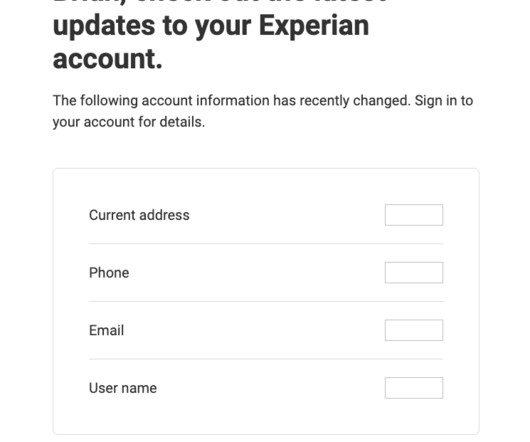
We have seen several high-profile accounts that were taken over on X (formerly Twitter) only to be used for cryptocurrency related promotional activities, like expressing the approval of exchange-traded funds (ETFs). The latest victim in this line-up is the Securities and Exchange Commission (SEC). You’re all set.


































Let's personalize your content