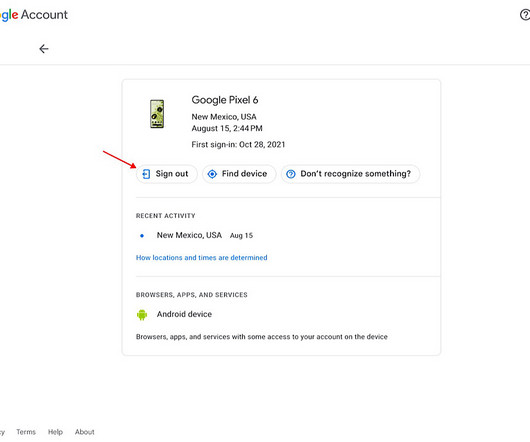
How to Remove a Lost Device From Your Google Account
Tech Republic Security
AUGUST 24, 2023
Follow this guide to learn how to easily remove any device from your Google account and keep your account secure.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.
Tech Republic Security
AUGUST 24, 2023
Follow this guide to learn how to easily remove any device from your Google account and keep your account secure.
Malwarebytes
JANUARY 10, 2024
We have seen several high-profile accounts that were taken over on X (formerly Twitter) only to be used for cryptocurrency related promotional activities, like expressing the approval of exchange-traded funds (ETFs). The latest victim in this line-up is the Securities and Exchange Commission (SEC). You’re all set.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Security Affairs
FEBRUARY 27, 2021
The telecommunications giant T-Mobile disclosed a data breach after some of its customers were apparently affected by SIM swap attacks. The telecommunications provider T-Mobile has disclosed a data breach after it became aware that some of its customers were allegedly victims of SIM swap attacks.

Identity IQ
JULY 3, 2023
How to Detect and Respond to Account Misuse IdentityIQ As digital connectivity continues to grow, safeguarding your online accounts from misuse is becoming increasingly crucial. Account misuse can result in alarming repercussions, including privacy breaches, financial losses, and identity theft.

Threatpost
JANUARY 16, 2020
iPhone users can now use Bluetooth to secure their Google accounts.

Malwarebytes
JUNE 14, 2021
Although sharing your day’s highlights in snapshots and videos on Instagram can be entertaining, some people claim to feel happier after deleting their accounts. If you do, remember that you will lose the following data permanently when you delete your Instagram account: Profile Photos Videos Comments Likes Followers.

Security Affairs
MARCH 13, 2020
Experts discovered an Android Trojan, dubbed Cookiethief , that is able to gain root access on infected devices and hijack Facebook accounts. “This way, a cybercriminal armed with a cookie can pass himself off as the unsuspecting victim and use the latter’s account for personal gain.”. ” continues Kaspersky.

Schneier on Security
DECEMBER 4, 2018
There are lots of articles about there telling people how to better secure their computers and online accounts. To remain anonymous and secure on the Internet, invest in a Virtual Private Network account, but remember, the bad guys are very smart, so by the time this column runs, they may have figured out a way to hack into a VPN.
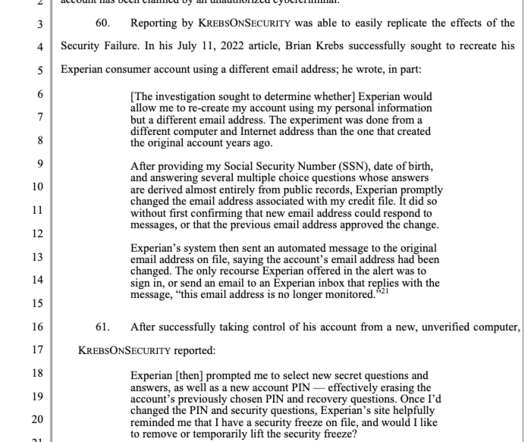
Krebs on Security
AUGUST 5, 2022
A class action lawsuit has been filed against big-three consumer credit bureau Experian over reports that the company did little to prevent identity thieves from hijacking consumer accounts. So had their passwords and account PIN and secret questions.

SecureWorld News
MAY 26, 2022
Federal Trade Commission (FTC) and the Department of Justice (DOJ) charged Twitter with a $150 million penalty for " deceptively using account security data for targeted advertising.". Twitter, like many other social media websites, asks users to provide their phone number and email address to better protect their account.

SecureWorld News
AUGUST 28, 2023
The emails in the campaign purported to be from Microsoft, and they claimed that the recipient needed to update their account security settings or activate two-factor authentication (2FA)/multi-factor authentication (MFA) within 72 hours.

eSecurity Planet
MARCH 8, 2022
The average internet user has somewhere around 100 accounts, according to NordPass research, meaning they have to track 100 different passwords or risk using the same one over and over. Users can share password files securely with encrypted transmissions. Event logs 24/7 support Security audit and compliance. Bitwarden Overview.

SecureWorld News
AUGUST 5, 2023
Multi-factor authentication (MFA) is a fundamental component of best practices for account security. It is a universal method employed for both personal and corporate user accounts globally. While MFA adds an extra security shield to accounts, deterring most cybercriminals, determined attackers can find ways to sidestep it.

Malwarebytes
OCTOBER 7, 2021
2SV adds an extra layer when logging into your account and the additional step happens after you’ve entered your password. It’s simple, and it dramatically decreases the chance of someone else accessing an account. We want to help keep your account safe & 2SV is an important step! Enable on your Google Account ?

Security Affairs
NOVEMBER 9, 2021
Robinhood disclosed a security breach, an unidentified threat actor gained unauthorized access to approximately 7 million customer records. is an American commission-free stock trading and investing platform, it had 18 million accounts as of March 2021, with over $80 billion in assets. Robinhood Markets , Inc.

Security Boulevard
MARCH 20, 2024
Over 12 years ago, I came across this new online security solution that let me look at my entire set of web and mobile transactions in real time, as the traffic came across the network. As the manager of online security, this was the best data I had ever seen. A Needed Defense Update appeared first on Security Boulevard.

Approachable Cyber Threats
JANUARY 24, 2022
Today, many people when they sign up for a new account for an internet-based service are asked to pick a password to help secure their account from unauthorized access. For instance, in securing your high risk accounts like banking or personal finance accounts, healthcare accounts, government services accounts (DMV, IRS, etc.),

Security Boulevard
APRIL 4, 2024
The post Google Chrome Enlists Emerging DBSC Standard to Fight Cookie Theft appeared first on Security Boulevard.
Thales Cloud Protection & Licensing
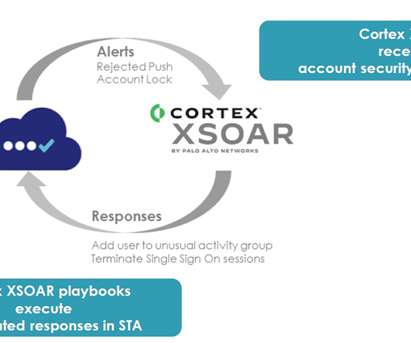
DECEMBER 8, 2021
During the Thales Trusted Access Summit 2021, Rishi Bhargava, VP, Product at Palo Alto Networks , and Dirk Strauch, NTT Data , and I discussed how security teams can leverage Cortex XSOAR and SafeNet Trusted Access to build a solid security posture for the enterprise. The need for access management automation. Benefits of the solution.

Hot for Security
JUNE 30, 2021
“These measures will help strengthen your account security and will help us better understand your needs.”. Creating a new developer account on the platform is now a little more complex, with a few extra steps that would discourage, hopefully, developers with malicious intent.

Hot for Security
JUNE 30, 2021
“These measures will help strengthen your account security and will help us better understand your needs.”. Creating a new developer account on the platform is now a little more complex, with a few extra steps that would discourage, hopefully, developers with malicious intent.

Approachable Cyber Threats
MARCH 24, 2023
However, with the increasing number of cyber threats lurking in the digital realm, protecting your social media accounts has become paramount. In this post, we will discuss the importance of securing your social media accounts and offer tips on how to keep your digital identity safe. Why should I secure my social media accounts?”

Approachable Cyber Threats
MARCH 24, 2023
However, with the increasing number of cyber threats lurking in the digital realm, protecting your social media accounts has become paramount. In this post, we will discuss the importance of securing your social media accounts and offer tips on how to keep your digital identity safe. Why should I secure my social media accounts?”
eSecurity Planet
APRIL 14, 2023
Malicious bots can be used to carry out a range of cyber threats like account takeovers and DDoS attacks, so bot protection is an increasingly important defense for web-facing assets. Comprehensive protection: DataDome protects against all types of bots, including credential stuffing, web scraping, and account takeover attacks.

Malwarebytes
FEBRUARY 12, 2021
Two former college graduates are in a lot of trouble after breaking into other students’ accounts and stealing sensitive personal data. Working with another former graduate, he accessed the school email accounts of dozens of college students and stole private nude photographs. What happened? Many of the images were then shared.
Google Security
MAY 11, 2022
Posted by Daniel Margolis, Software Engineer, Google Account Security Team Every year, security technologies improve: browsers get better , encryption becomes ubiquitous on the Web , authentication becomes stronger. Even though security keys work great, we don't expect everyone to add one to their keyring.

Malwarebytes
SEPTEMBER 21, 2021
Whether you’re looking for a smartphone, a laptop, a gaming device or something else, or even just signing up for an account online, you want to make sure your kids are protected. Keep your online accounts secure. You need to put in as much friction as possible in order to protect your kids’ accounts.
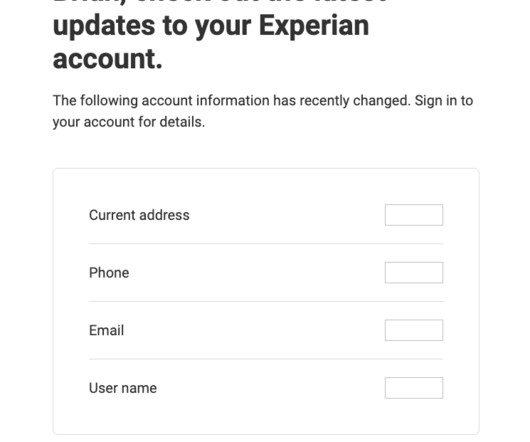
Krebs on Security
NOVEMBER 11, 2023
In the summer of 2022, KrebsOnSecurity documented the plight of several readers who had their accounts at big-three consumer credit reporting bureau Experian hijacked after identity thieves simply re-registered the accounts using a different email address. So once again I sought to re-register as myself at Experian.

Duo's Security Blog
NOVEMBER 23, 2020
MFA provides layered defense and peace of mind." – Gautam Vij, CRO of FEITIAN Technologies US Duo’s MFA For All Scenarios Duo offers eight different MFA methods , including mobile apps, push notifications, offline options, WebAuthn, security keys, and more.
Security Boulevard
JANUARY 2, 2024
The post Google Whistles While OAuth Burns — ‘MultiLogin’ 0-Day is 70+ Days Old appeared first on Security Boulevard. What a Mickey Mouse operation: Infostealer scrotes having a field day with unpatched vulnerability.

Krebs on Security
NOVEMBER 6, 2018
that has been tracking down individuals engaged in unauthorized “SIM swaps” — a complex form of mobile phone fraud that is often used to steal large amounts of cryptocurrencies and other items of value from victims. In early July 2018, Ferri was traveling in Europe when he discovered his T-Mobile phone no longer had service.

Google Security
MAY 3, 2023
By: Arnar Birgisson and Diana K Smetters, Identity Ecosystems and Google Account Security and Safety teams Starting today , you can create and use passkeys on your personal Google Account. Choosing strong passwords and remembering them across various accounts can be hard. Passkeys help address all these issues.

Approachable Cyber Threats
JANUARY 12, 2022
While LastPass may not have suffered a breach, it should be a wake up call to many who still use single-factor password-based authentication to their LastPass accounts and password vaults to do a little housekeeping. Credential stuffing is a tactic hackers commonly use to compromise internet accounts. What is LastPass?”

SecureList
OCTOBER 13, 2023
The user creates an account and gains access to the bot. Account hacking. Account security is always a priority issue. It is quite possible for attackers to gain access to employee accounts — and the data in them — for example, through phishing attacks or credential stuffing.

eSecurity Planet
MARCH 10, 2022
And if you use the same password for all of your online accounts, you’re giving attackers access to a ton of information with very little work. Password managers , like Keeper and 1Password, make it easy for users to secure their online accounts without having to remember a different password for each of their accounts.

Heimadal Security
AUGUST 4, 2021
Ransomware trends are on the rise, even more so today than in the previous years. According to some estimates, by end of 2021, the number of ransomware attacks would have increased to 1 every 11 seconds, the outstanding record being one ransomware every 14 seconds.

Troy Hunt
NOVEMBER 14, 2018
If someone obtains the thing that you know then it's (probably) game over and they have access to your account. Indeed, when you store your TOTP secret in the same place that you keep your password for a site, you do not have second factor security. It's most damaging when account recovery can be facilitated via SMS alone (i.e.

Spinone
MARCH 25, 2019
There are quite a few things that can be done to greatly improve the security of Google Drive, in general, using both built-in technologies provided by Google as well as practical steps. This splitting up of the required components of authentication helps to bolster the security of your Google account.

eSecurity Planet
MARCH 30, 2023
million active endpoints 1,000 user identity or endpoint identity groups Security Qualifications Cisco has obtained government certification for ISE related to FIPS 140 2 validated cryptographics , Common Criteria certification, and inclusion in the Unified Capabilities approved list.

Malwarebytes
MAY 14, 2021
There was a time when stolen gaming accounts were almost treated as a fact of life. Security research in this area was occasionally derided as unimportant or trivial. When sign-up rates for something as common as Google accounts are struggling to hit double figures , it’s definitely a concern.

eSecurity Planet
MAY 6, 2021
Additionally, both vendors have easy-to-use mobile applications that make it a breeze to access accounts securely while traveling. Dashlane and LastPass both boast strong security profiles. Dashlane also offers a free Premium Personal account for Team users and Premium Family account for Business users.

SC Magazine
MAY 3, 2021
Being introduced to the account manager as well… is very helpful to us to really understand what the personalities are,” he added. If you’re at GM, you want to go back to Chrysler or somebody else that’s a large corporation like a Mobil Corporation,” and seek out their input on the product. You can’t just walk away after the sale. “A

ForAllSecure
OCTOBER 29, 2020
In this episode of The Hacker Mind, Dr. Jared DeMott of VDA Labs talks about his work securing voter registration tablets and also about the prospects for downloadable, safe voting applications on your preferred mobile device in the future. Bee: I have to put in 16 letters and digits to get into my FreshDirect account.

ForAllSecure
OCTOBER 29, 2020
In this episode of The Hacker Mind, Dr. Jared DeMott of VDA Labs talks about his work securing voter registration tablets and also about the prospects for downloadable, safe voting applications on your preferred mobile device in the future. Bee: I have to put in 16 letters and digits to get into my FreshDirect account.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content