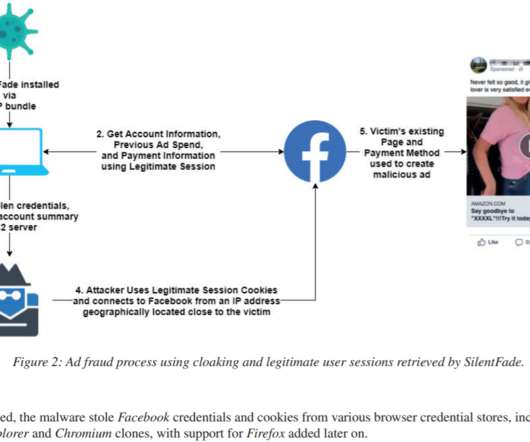
Bogus Chat GPT extension takes over Facebook accounts
Malwarebytes
MARCH 26, 2023
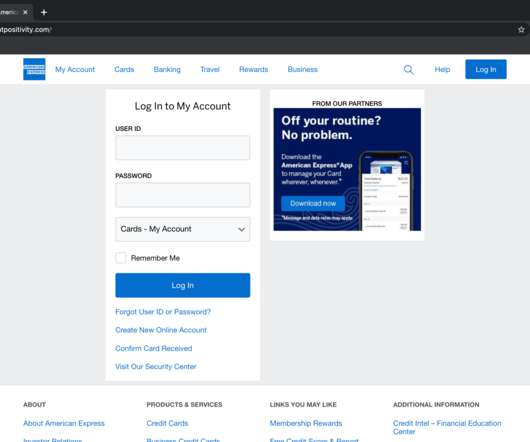
There’s some bad things lurking in search engine results waiting to compromise your Facebook account. This site eventually directs you to a Chrome extension download from the official extension store. However, the real aim of the game here is to compromise Facebook accounts. Check developer authenticity.









































Let's personalize your content