FBI, Dutch Police Disrupt ‘Manipulaters’ Phishing Gang
Krebs on Security
JANUARY 31, 2025
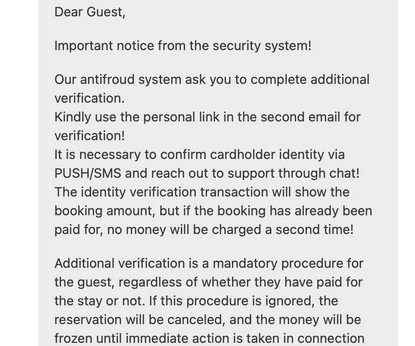
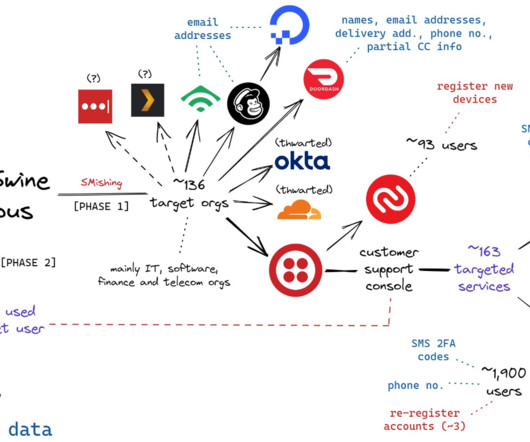
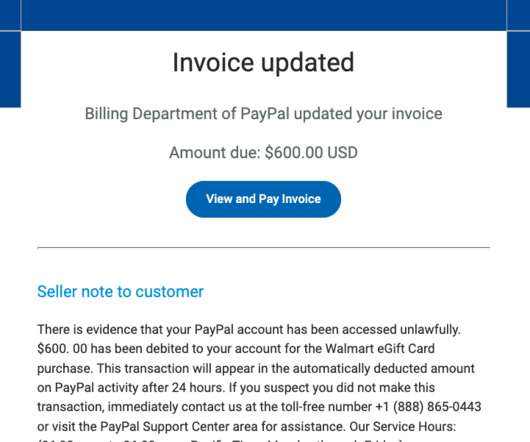
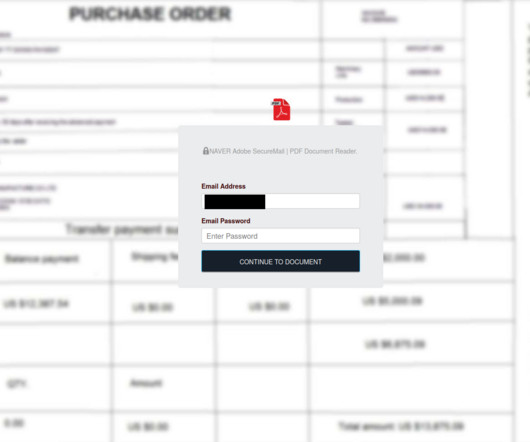
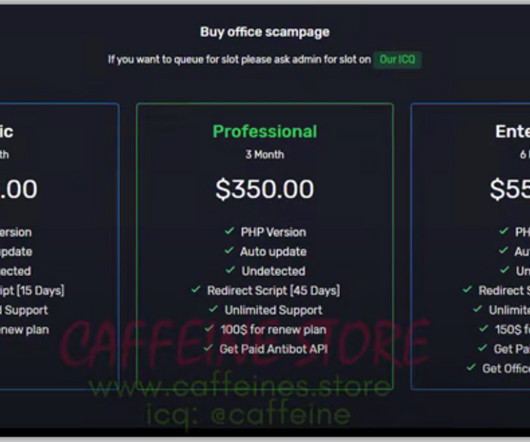
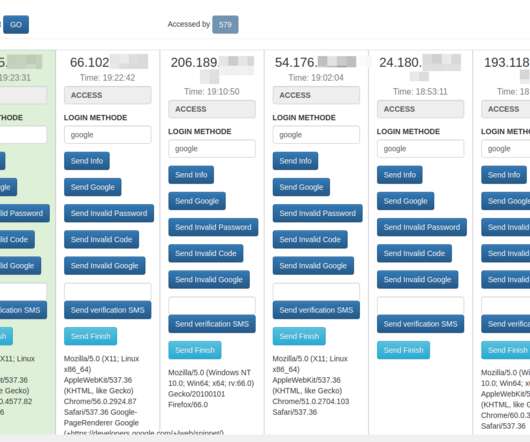
Department of Justice refers to the cybercrime group as Saim Raza , after a pseudonym The Manipulaters communally used to promote their spam, malware and phishing services on social media. ” Manipulaters advertisement for Office 365 Private Page with Antibot phishing kit sold via Heartsender. Image: DomainTools.








































Let's personalize your content