How social engineering is related to Cybersecurity
CyberSecurity Insiders
MAY 1, 2023
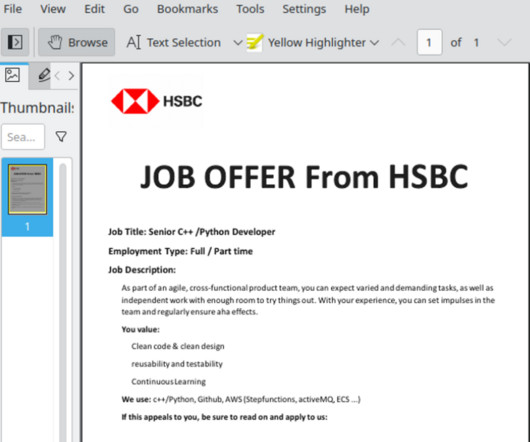
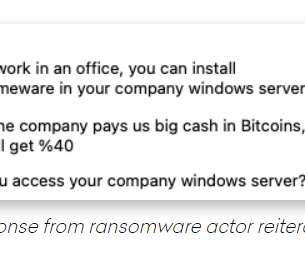
Social engineering is a term used to describe the manipulation of people into revealing sensitive information or performing actions that they otherwise wouldn’t. Social engineering is an age-old tactic that is often used in phishing attacks. In conclusion, social engineering is a significant threat to cybersecurity.














































Let's personalize your content