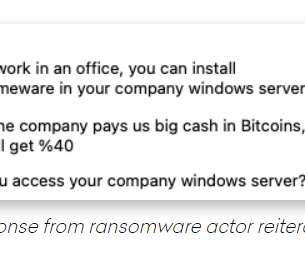
Ransomware Groups Look for Inside Help
eSecurity Planet
AUGUST 23, 2021
Ransomware attackers, who use myriad methods to get their malware into the systems of businesses large and small in hopes of pulling down millions of dollars, are now going directly to the source. Evolving Ransomware Scene. million ransomware attacks in the first six months of 2021, compared with 121.5 There were 304.7




































Let's personalize your content