NEW TECH: This free tool can help gauge, manage third-party cyber risk; it’s called ‘VRMMM’
The Last Watchdog
JANUARY 30, 2019
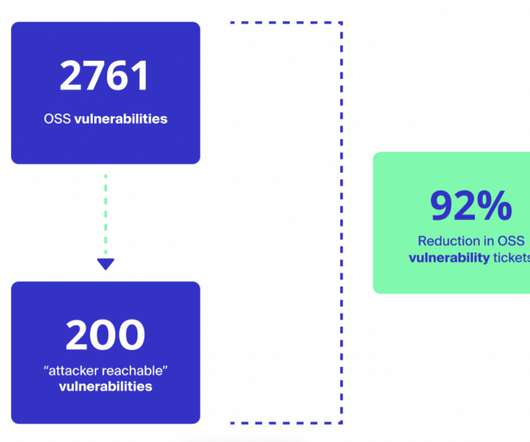
Related: Atrium Health breach highlights third-party risks. Third-party cyber risks are likely to persist at the current scale for a while longer. According to a recent Ponemon Institute study , some 59% of companies experienced a third-party data breach in 2018, yet only 16% believe they are effectively mitigating third-party risk.





















Let's personalize your content