New Coronavirus-themed malspam campaign delivers FormBook Malware
Security Affairs
MARCH 8, 2020
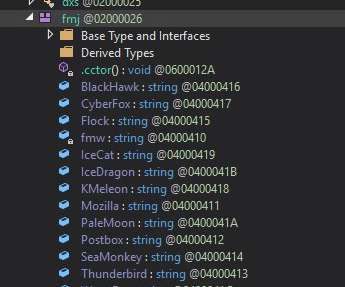
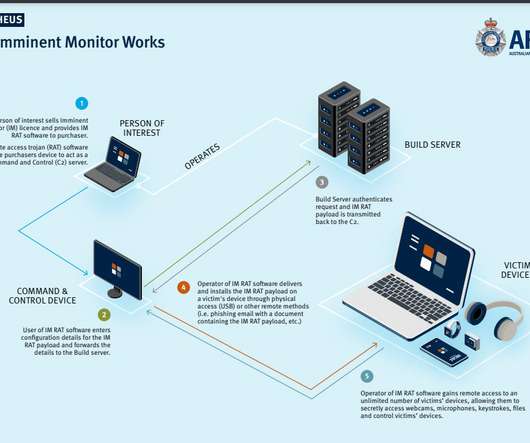
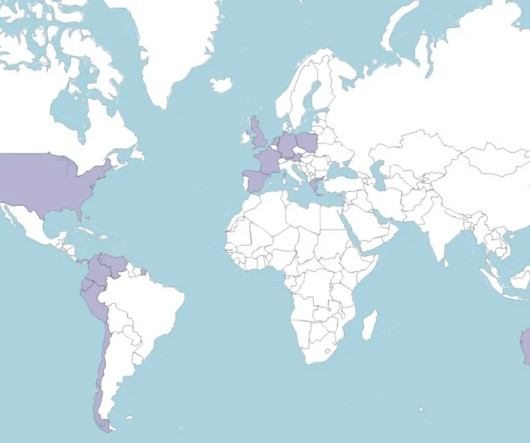
Experts uncovered a new Coronavirus (COVID-19 ) -themed campaign that is distributing a malware downloader that delivers the FormBook information-stealing Trojan. Experts at MalwareHunterTeam uncovered a new malspam campaign exploiting the fear in the Coronavirus (COVID-19) to deliver malware. states the analysis published by FireEye.























Let's personalize your content