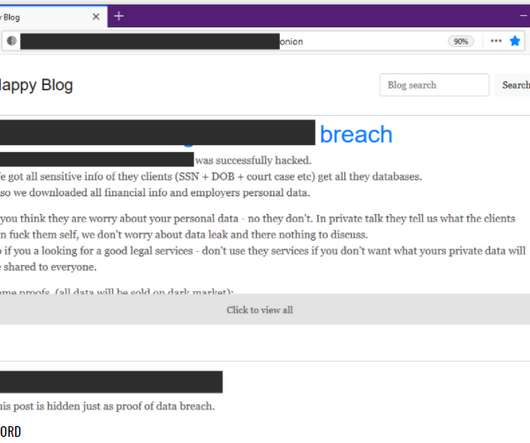
Data of 21 Million VPN users breached
Quick Heal Antivirus
MARCH 18, 2021
VPN is a prominent tool for enhanced online life. VPN consists of a tunnel that your encrypted data. The post Data of 21 Million VPN users breached appeared first on Quick Heal Blog | Latest computer security news, tips, and advice.



































Let's personalize your content