Security Affairs newsletter Round 364 by Pierluigi Paganini
Security Affairs
MAY 8, 2022
If you want to also receive for free the newsletter with the international press subscribe here.

Security Affairs
MAY 8, 2022
If you want to also receive for free the newsletter with the international press subscribe here.
eSecurity Planet
SEPTEMBER 15, 2022
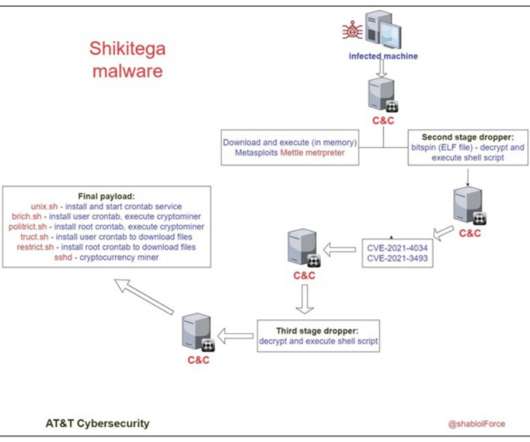
The researchers said the attackers have encoded the final payload with several layers, requiring several loops of decoding before it gets deployed, making it impossible to detect by signature-based antivirus solutions. Five Scripts Provide Persistence. Cybercriminals Use C2 Servers to Deploy Cryptominer. Shikitega installs XMRig version 6.17.0
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

eSecurity Planet
JUNE 16, 2022
Also read: Best Antivirus Software of 2022. There are many types of cyberattacks , with top trends for 2022 including mobile attacks, ransomware, COVID-related scams and hacks, zero-click attacks , malicious QR codes , phishing , cryptojacking , and IoT malware attacks, among others. Cyberattack Statistics. Ransomware. Other methods.

CyberSecurity Insiders
SEPTEMBER 21, 2021
The campaign uses multiple shell/batch scripts, new open source tools, a cryptocurrency miner, the TeamTNT IRC bot, and more. As of August 30, 2021, many malware samples still have zero antivirus (AV) detections and others have low detection rates. Windows component – Set up a cryptocurrency miner. Background.

eSecurity Planet
FEBRUARY 16, 2021
For access to the decryption key, the victim must make prompt payment, often in cryptocurrency shielding the attacker’s identity. This is especially true for your existing intrusion detection and prevention system (IDPS), antivirus, and anti-malware. Bitdefender : Bitdefender Antivirus Plus. Offline Backups. Description.

SecureList
MAY 31, 2021
For now, we can tentatively assume that the growth in cryptocurrency prices, in particular bitcoin, has attracted the attention of cybercriminals and returned miners to their toolkit. IoT attacks. IoT threat statistics. Number of unique users attacked by miners, Q1 2021 ( download ). Trojan-Downloader.Shell.Agent.p.
Security Affairs
AUGUST 27, 2020
Most of us already know the importance of using antivirus , anti-malware, and VPNs to secure our computers, phones, and other devices against potential attacks. To perform the experiment, we used Internet of Things (IoT) search engines to search for open devices that utilized common printer ports and protocols. Original post: [link].
Let's personalize your content