Work from Home leading to surge in Cyber Attacks in UK
CyberSecurity Insiders
JANUARY 30, 2022
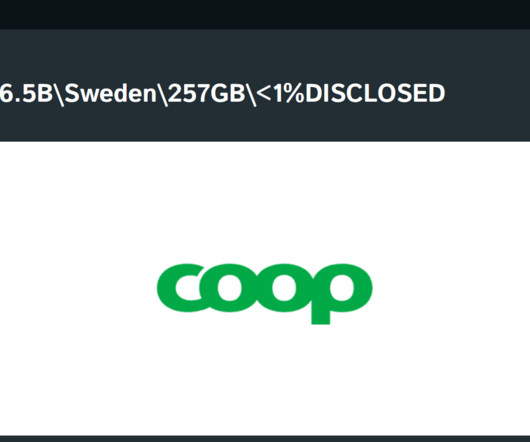
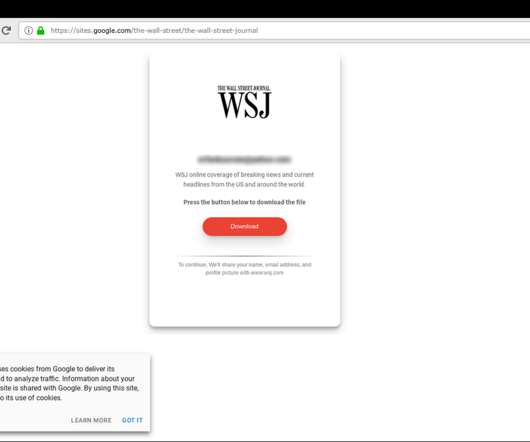
The Work from Home (WfH) culture might do well to the employees, but some companies are disclosing openly that they are witnessing a surge in cyber attacks( mainly data breaches) on their IT infrastructure as their employees are not following basic cyber hygiene of using strong passwords and authenticating their Identity whole accessing networks.











































Let's personalize your content