The Evolving Landscape of Cybersecurity: Trends and Challenges
CyberSecurity Insiders
JUNE 1, 2023
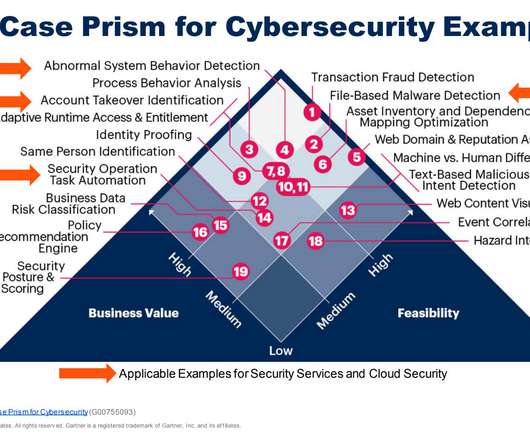
In today’s interconnected world, where technology permeates every aspect of our lives, ensuring robust cybersecurity has become an utmost priority. Artificial Intelligence (AI) and Machine Learning (ML) in Cybersecurity: AI and ML are transforming the way we approach cybersecurity.


































Let's personalize your content