12 Data Loss Prevention Best Practices (+ Real Success Stories)
eSecurity Planet
APRIL 12, 2024
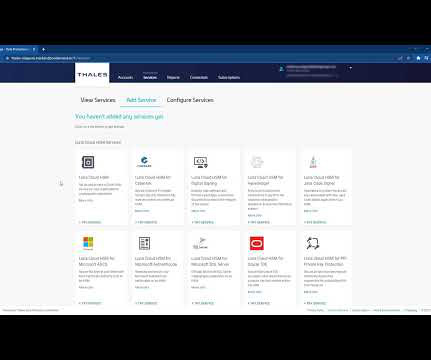
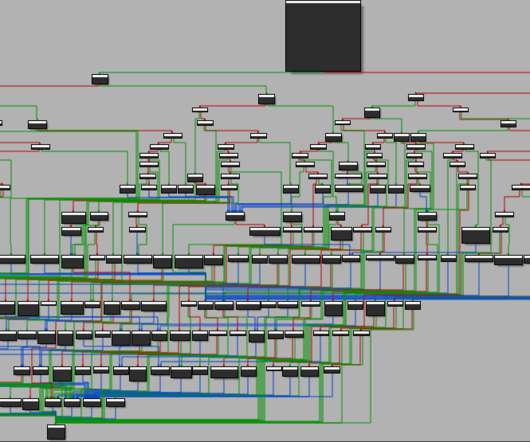
Sample access restriction from SolarWinds’ access rights management dashboard Encrypt Data This practice entails using data encryption tools to keep sensitive data confidential and safe from illegal access or exploitation, even if the device is lost or stolen. No user data was lost.










































Let's personalize your content