Sophos to put an end to TLS based Cyber Attacks
CyberSecurity Insiders
APRIL 25, 2021
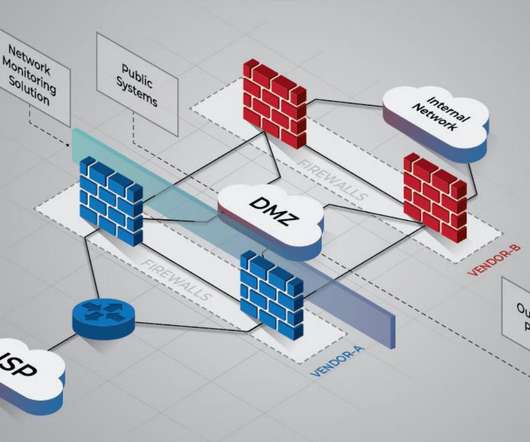
Cybersecurity firm Sophos has come up with a solution that promises to put an end to TLS based cyber attacks. Its XGS Series Firewall appliance does a Transport Layer Security (TLS) inspection that is 5 times faster than what the other models offer.







































Let's personalize your content