StripedFly: Perennially flying under the radar
SecureList
OCTOBER 25, 2023
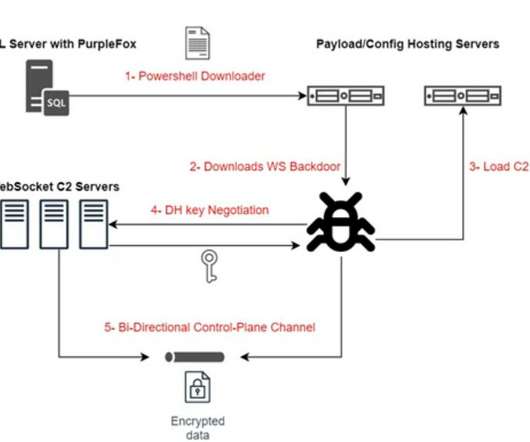
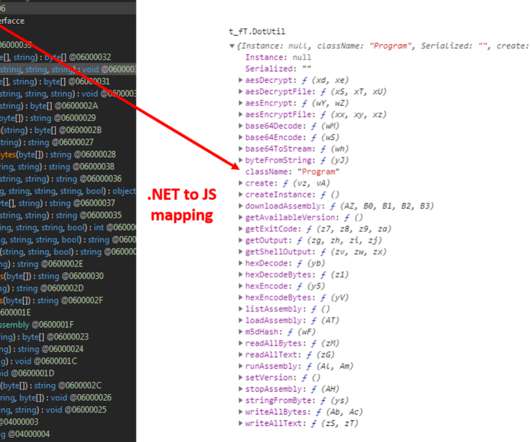
Introduction It’s just another cryptocurrency miner… Nobody would even suspect the mining malware was merely a mask, masquerading behind an intricate modular framework that supports both Linux and Windows. This malware employed a custom EternalBlue SMBv1 exploit to infiltrate its victims’ systems.










































Let's personalize your content