Cuttlefish malware targets enterprise-grade SOHO routers
Security Affairs
MAY 1, 2024
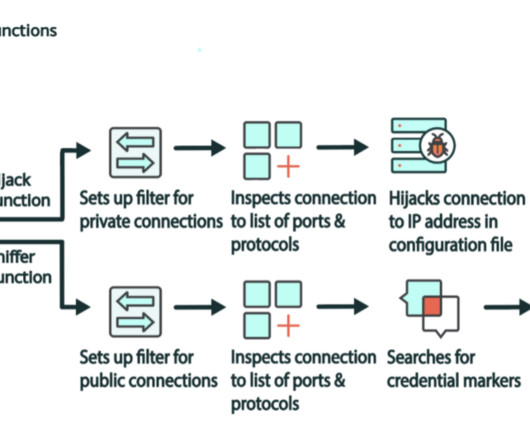
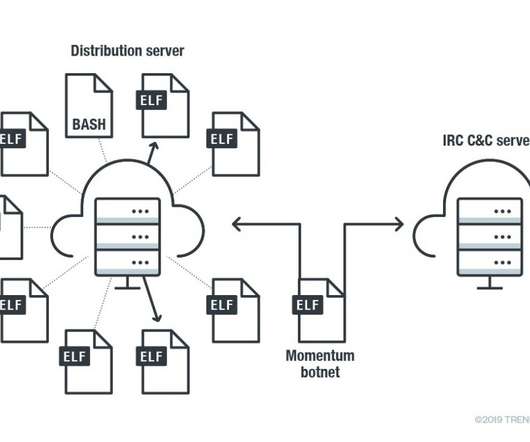
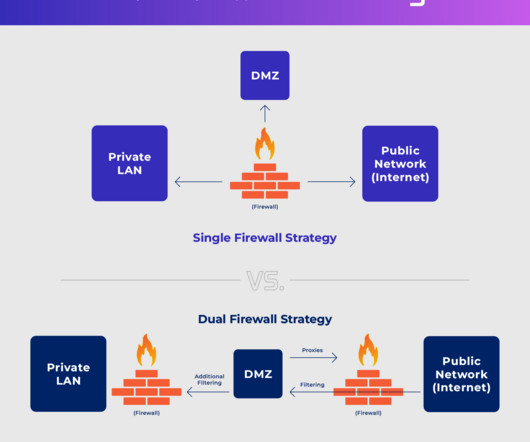
Researchers at Lumen’s Black Lotus Labs discovered a new malware family, named Cuttlefish, which targets enterprise-grade and small office/home office (SOHO) routers to harvest public cloud authentication data from internet traffic. The malicious code can also perform DNS and HTTP hijacking within private IP spaces.





















Let's personalize your content