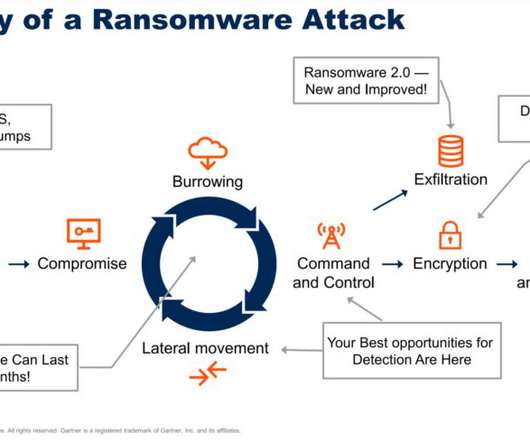
Top Four Steps to Reduce Ransomware Risk
Tech Republic Security
JULY 24, 2022
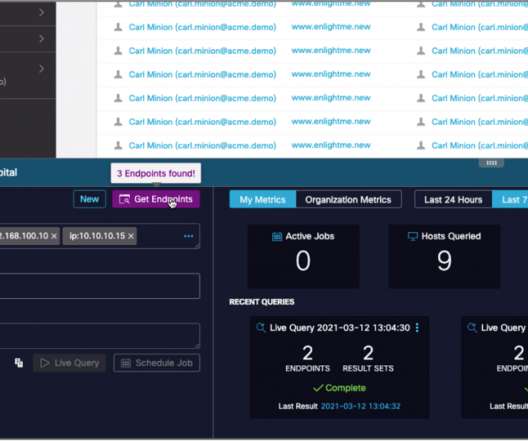
IT leaders must integrate security tools into a cooperative, consolidated ecosystem using a composable and scalable cybersecurity mesh architecture (CSMA) approach. The post Top Four Steps to Reduce Ransomware Risk appeared first on TechRepublic. By 2024, organizations adopting a CSMA to integrate security tools to.













































Let's personalize your content