Does a VPN Slow Down Your Internet Speed?
Tech Republic Security
MAY 16, 2024
Can a VPN slow down your internet? Find out how VPNs can impact your internet speed with our article.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Tech Republic Security
MAY 16, 2024
Can a VPN slow down your internet? Find out how VPNs can impact your internet speed with our article.

Schneier on Security
AUGUST 25, 2021
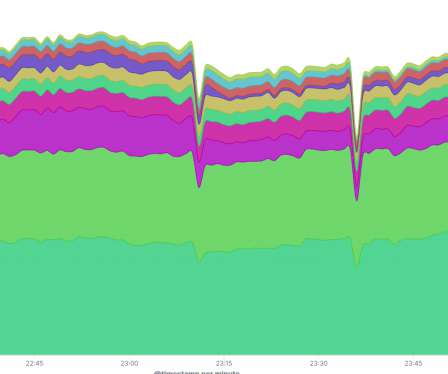
Vice has an article about how data brokers sell access to the Internet backbone. It’s useful for cybersecurity forensics, but can also be used for things like tracing VPN activity. This is netflow data. At a high level, netflow data creates a picture of traffic flow and volume across a network.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Troy Hunt
APRIL 6, 2020
I also have an article on [thing] and I think it would be a great addition to your blog. So now when people search for [thing], they'll hopefully end up here rather than on the spammy article thus penalising you for your behaviour. No, no it wouldn't and there are all sorts of reasons why not.

SecureBlitz
FEBRUARY 10, 2021
This article shows our result of the full practical evaluation and review of the Private Internet Access (PIA) VPN. What Is A VPN? Virtual Private Network (VPN) is a service that continually changes your IP address to a Secure Server to keep you anonymous when browsing.

Identity IQ
OCTOBER 17, 2023
Should You Always Use a VPN? IdentityIQ Using a virtual private network (VPN) can help keep you safe and anonymous online. It’s a good idea to always keep your VPN active for maximum protection, but there are certain scenarios when you might need to temporarily shut it off. Here’s what you need to know about VPNs.

CyberSecurity Insiders
AUGUST 6, 2021
VPNs allow tremendous liberty when it comes to network and data protection and, as such, are necessary for every internet consumer, business, and entertainment alike. Using VPNs comes with many benefits and should be something that most users should take advantage and put to use. Reasons why everyone needs to use VPNs.
Identity IQ
AUGUST 19, 2023
7 Internet Safety Tips for Safer Internet Browsing IdentityIQ With the internet, we can access vast amounts of information with only a click or tap. This year, the total number of internet users worldwide reached 5.18 And as immense as the internet is, so are the risks. Many threats lurk in its corners.

Identity IQ
APRIL 22, 2021
If you want to help secure your digital identity, a virtual private network (VPN) is a great tool you can use for added online privacy. In this guide, we discuss VPNs in detail, including how they work, how they protect you and why you should use one when browsing the web. What is a VPN? How does a VPN Work?

Malwarebytes
MAY 7, 2021
A Virtual Private Network (VPN) creates a safe “tunnel” between you and a computer you trust (normally your VPN provider) to protect your traffic from spying and manipulation. Any VPN worth its money encrypts the information that passes through it, so in this article we will ignore those that don’t use encryption.

SecureBlitz
JANUARY 19, 2022
Are you interested in knowing the best VPN for Zepeto? If yes, then you will get them on this article today. The post 5 Best VPN for Zepeto [2022 LIST] appeared first on SecureBlitz Cybersecurity. Zepeto is an application that allows its users to create 3D animated versions of themselves.

eSecurity Planet
DECEMBER 23, 2020
As a result, companies are relying on virtual private networks (VPNs) , which establish encrypted connections to enterprise applications over the public internet, to connect their workforce. These VPN endpoints are typically set up to support 5 to 10 percent of a company’s workforce at any given time. Enhance VPN Security.

Krebs on Security
DECEMBER 2, 2021
28, other Ubiquiti employees spotted the unusual downloads, which had leveraged internal company credentials and a Surfshark VPN connection to hide the downloader’s true Internet address. The message was sent through an IP address associated with the same Surfshark VPN.

Hackology
JULY 3, 2023
Sometimes external factors like internet censorship and state censorship can limit the public’s access to this essential service. In this article, we will explore what is WhatsApp proxy, how you can use them to bypass internet shutdown restrictions, and the benefits they bring. billion users. Let’s begin! Well, don’t worry.

CyberSecurity Insiders
MAY 4, 2023
The internet has transformed our lives in many positive ways, but it has also created a new set of challenges, such as the need to protect our privacy online. With so much personal infor-mation available on the internet, it is important to take steps to safeguard our privacy.

Schneier on Security
DECEMBER 4, 2018
There are lots of articles about there telling people how to better secure their computers and online accounts. While I agree with some of it, this article contains some particularly bad advice: 1. I think twice about accessing my online bank account from a pubic Wi-Fi network, and I do use a VPN regularly.

Schneier on Security
APRIL 7, 2020
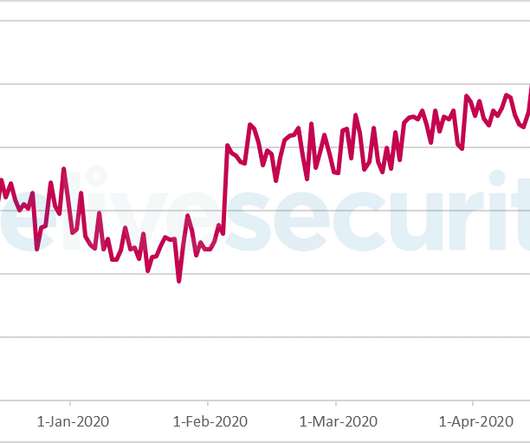
If the organization is lucky, they will have already set up a VPN for remote access. Handing people VPN software to install and use with zero training is a recipe for security mistakes, but not using a VPN is even worse. Three, employees are more likely to access their organizational networks insecurely.
Security Affairs
JANUARY 13, 2024
Every week the best security articles from Security Affairs are free for you in your email box. A new round of the weekly SecurityAffairs newsletter arrived! Enjoy a new round of the weekly SecurityAffairs newsletter, including the international press.
Malwarebytes
AUGUST 25, 2021
How many free articles have they read. You can also tighten your privacy by using a Virtual Private Network (VPN) to anonymize your traffic. You have options here, since you can install a VPN to anonymize all your Internet traffic, or you can install a VPN extension that will do so for your browser only.

Malwarebytes
JANUARY 22, 2023
Article 8 of the Human Rights Act protects your right to respect for your private and family life. Check your browser settings Your browser is your gateway to the internet. You can also tighten your privacy by using a Virtual Private Network (VPN) to anonymize your traffic. Privacy is a right that is yours to value and defend.

CyberSecurity Insiders
JUNE 5, 2023
In an increasingly connected world, where our lives revolve around the internet, safeguarding our privacy online has become paramount. In this article, we will explore actionable steps to protect your privacy online and ensure a safer digital presence. It masks your IP address and helps maintain your anonymity online.

Identity IQ
MARCH 9, 2023
IdentityIQ We rely on the internet, from communicating with loved ones on social media to working and conducting business. If you can connect to the network without a password, open your web browser and see if you can browse the internet. Use a VPN A VPN encrypts your traffic with military-grade encryption.

SecureList
APRIL 22, 2024
In our previous article , we described tools for collecting and exfiltrating files ( LoFiSe and PcExter ). Note that all tools described in this article are applied at the stage where the attackers have compromised high-privileged user credentials allowing them to connect to remote hosts.

CSO Magazine
JUNE 30, 2021
New research from Sophos finds 46% of malware communicating with a remote system over the Internet is utilizing TLS encryption to conceal communications and evade detection. TLS has historically served as the underpinning for VPN technology. To read this article in full, please click here

SecureWorld News
MARCH 10, 2022
Many threats that have until now been theoretical—like creation of a "Ru-net" as an alternative to the Internet—are becoming a reality. Cutting off Internet access to a country the size of Texas is not as simple as cutting a few cables or bombing a few cell towers. There are many tech angles to the war in Ukraine.
Security Affairs
JULY 22, 2023
through 4.73, VPN series firmware versions 4.60 The researchers warned that as of May 19, there were at least 42,000 instances of Zyxel devices on the public internet. Since the vulnerability is in the VPN service, which is enabled by default on the WAN, we expect the actual number of exposed and vulnerable devices to be much higher.”

Security Affairs
OCTOBER 17, 2023
Sandworm were observed targeting open ports and unprotected RDP or SSH interfaces to gain access to the internet-facing systems. ’ The CERT-UA also reported that the state-sponsored hackers used compromised VPN accounts that weren’t protected by multi-factor authentication. “Note (!) .’ “Note (!)

Security Affairs
JANUARY 15, 2023
Every week the best security articles from Security Affairs free for you in your email box. Most internet-exposed Cacti servers exposed to hacking French CNIL fined Tiktok $5.4 Most internet-exposed Cacti servers exposed to hacking French CNIL fined Tiktok $5.4 A new round of the weekly SecurityAffairs newsletter arrived!

Identity IQ
JUNE 3, 2021
Every move you make on the internet can be seen by your internet service provider, or ISP. Discover why your ISP is tracking you, what they can see, and how you can get more privacy while browsing the internet. Once you connect to the internet, your ISP assigns an IP address to your connection. Use A VPN.

eSecurity Planet
APRIL 15, 2024
Threats range from severe weaknesses in Ivanti’s VPN appliances to zero-day exploits in popular software such as Palo Alto Networks’ PAN-OS and Telegram’s Windows client. Check out our article on SaaS security checklist and learn how to create one. It’s suggested that automatic updates be enabled.

SiteLock
AUGUST 27, 2021
Simply defined, the internet of things (IoT) is a network of Internet-connected objects able to collect and exchange data. To help avoid these online risks, it is highly recommended to use a Virtual Private Network (VPN). VPNs are the baseline cybersecurity tool to safeguard internet-enabled devices and a home network.

Malwarebytes
DECEMBER 21, 2022
In an online article the newspaper published an internal statement from the chief executive and the editor-in-chief that says: “We believe this to be a ransomware attack but are continuing to consider all possibilities.” Limit internet access to critical devices and systems where possible. The suspected cause is ransomware.

Identity IQ
NOVEMBER 2, 2023
This article reviews the advantages of IdentityIQ and presents some alternatives to canceling to help you make an informed decision. VPN and Antivirus IdentityIQ gives you access to Bitdefender® Total Security VPN and antivirus software to enhance your online security. We also guide you through how to cancel IdentityIQ services.
Security Affairs
APRIL 28, 2020
The 21st of March, the website received a Denial of Service attack after the publishing of an article about Mubariz Mansimov, a businessman who has been imprisoned and claims that the arrest was ordered by the head of SOCAR – State Oil Company of Azerbaijan Rovnag Abdullayev and his cousin Anar Alizade. According to Article 13.3

CyberSecurity Insiders
MARCH 21, 2023
With the increasing need for online privacy and security, Virtual Private Networks (VPNs) have become a popular solution for internet users. VPNs allow users to access the internet securely and privately by encrypting their internet traffic and hiding their IP addresses. What is a VPN?

Hacker's King
JUNE 25, 2023
In cyber security and hacking, we usually have to do port forwarding (exposing your local port on the Internet) to make our network, application, or program available for everyone outside your local network (LAN to WAN). LocaltoNet LocaltoNet provides users with a secure tunnel for testing and hosting webpages on the Internet.

Identity IQ
NOVEMBER 6, 2023
Use Secure Websites (for Santa-Approved Shopping) When hunting for those perfect holiday deals, it’s essential to make sure you’re practicing safe internet browsing by shopping on secure websites. 5 Holiday Online Shopping Safety Tips 1. Avoid shopping on public Wi-Fi whenever you can.

Identity IQ
AUGUST 3, 2022
Internet protocol address, aka an IP address, is a unique number assigned to every computer and device that connects to the web so they can communicate with each other and share information. You can think of your IP address as a unique identifying label for your computer or device on the internet. Can I Hide My Address without a VPN?

Identity IQ
NOVEMBER 15, 2022
IdentityIQ plans also feature device security with anti-virus and VPN. You receive three-bureau credit reports and scores; real-time fraud alerts; identity monitoring; identity theft insurance; anti-virus and VPN; and other benefits. Device Security with Anti-Virus and VPN. So, you have complete protection. 1 in the industry.

CyberSecurity Insiders
JANUARY 19, 2023
In the first two blogs in this series, we discussed properly setting up IAM and avoiding direct internet access to AWS resources. Note : an exception to this statement is if the generation of encryption keys occurs over a publicly available Internet connection (e.g., coffee shop WiFi). ” What Is AWS Certificate Manager?

Malwarebytes
JUNE 3, 2022
Welcome to Internet Safety Month, a once-a-year event in which you, the public, are told that anywhere between three and 30 different best practices will simplify your approach to staying safe online. This year, then, for Internet Safety Month, we’re packaging our advice a little differently. Do use a VPN on public WiFi connections.
Security Affairs
JUNE 29, 2020
Below the recommendations provided by ESET on how to configure remote access correctly: Disable internet-facing RDP. If that is not possible, minimize the number of users allowed to connect directly to the organization’s servers over the internet. Require strong and complex passwords for all accounts that can be logged into via RDP.

Security Affairs
APRIL 8, 2022
In this article, we will discuss 15 of the most important cybersecurity measures. When you access the internet through a VPN, your data is encrypted and routed through a secure tunnel. VPNs are especially important if you use public Wi-Fi, as these networks are often unsecured and easy for hackers to exploit.

SiteLock
AUGUST 27, 2021
Whether it’s the local coffee shop or co-working space, the availability of an internet connection wherever we go has helped foster a growing segment of remote employees. Connecting to the internet is something we do every day. Use a Virtual Private Network (VPN). How to Find and Use a VPN Service.

Security Affairs
SEPTEMBER 27, 2020
Every week the best security articles from Security Affairs free for you in your email box. fitness chains Town Sports leaked online Group-IB detects a series of ransomware attacks by OldGremlin HOW DO PROVIDERS IMPLEMENT INTERNET BLOCKING IN BELARUS? A new round of the weekly SecurityAffairs newsletter arrived!
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content