Does a VPN Slow Down Your Internet Speed?
Tech Republic Security
MAY 16, 2024
Can a VPN slow down your internet? Find out how VPNs can impact your internet speed with our article.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Tech Republic Security
MAY 16, 2024
Can a VPN slow down your internet? Find out how VPNs can impact your internet speed with our article.

Troy Hunt
APRIL 6, 2020
I also have an article on [thing] and I think it would be a great addition to your blog. So now when people search for [thing], they'll hopefully end up here rather than on the spammy article thus penalising you for your behaviour. No, no it wouldn't and there are all sorts of reasons why not. kthanksbye!
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Identity IQ
OCTOBER 17, 2023
Should You Always Use a VPN? IdentityIQ Using a virtual private network (VPN) can help keep you safe and anonymous online. It’s a good idea to always keep your VPN active for maximum protection, but there are certain scenarios when you might need to temporarily shut it off. Here’s what you need to know about VPNs.
Security Boulevard
JUNE 17, 2022
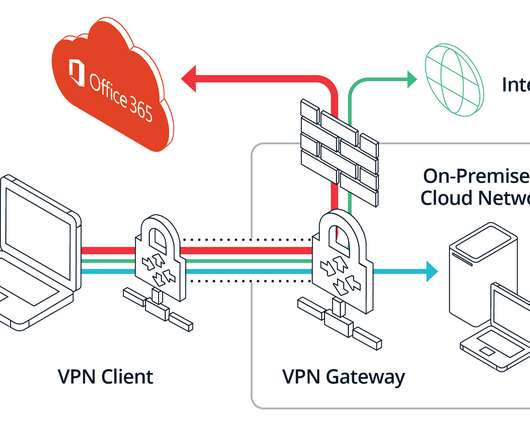
Does your enterprise security model require backhauling traffic destined for SaaS applications through corporate VPN gateways or concentrators? The post Article 1/5: Stop Using VPNs and IP Whitelists to Secure Access to SaaS Applications first appeared on Banyan Security.

CSO Magazine
NOVEMBER 3, 2022
A new espionage campaign, dubbed SandStrike, has been detected using malicious VPN apps to load spyware on Android devices, cybersecurity company Kaspersky reports. To read this article in full, please click here

CyberSecurity Insiders
AUGUST 6, 2021
Therefore, this article will look at various reasons why everyone should use VPNs. Reasons why everyone needs to use VPNs. Most VPNs are user-friendly and are created with well-detailed guides which are navigable by nearly anyone, even a technology illiterate individual. They are easy to use. Faster internet speed.

SecureBlitz
JANUARY 19, 2022
Are you interested in knowing the best VPN for Zepeto? If yes, then you will get them on this article today. The post 5 Best VPN for Zepeto [2022 LIST] appeared first on SecureBlitz Cybersecurity. Zepeto is an application that allows its users to create 3D animated versions of themselves.

CSO Magazine
APRIL 21, 2022
And as the war in Ukraine continues, more people are turning to VPNs to get around blocks imposed by Russia and other authoritarian governments, such as that shown by Cloudflare’s data on VPN usage. To read this article in full, please click here

Malwarebytes
MAY 7, 2021
A Virtual Private Network (VPN) creates a safe “tunnel” between you and a computer you trust (normally your VPN provider) to protect your traffic from spying and manipulation. Any VPN worth its money encrypts the information that passes through it, so in this article we will ignore those that don’t use encryption.

SecureBlitz
FEBRUARY 10, 2021
This article shows our result of the full practical evaluation and review of the Private Internet Access (PIA) VPN. What Is A VPN? Virtual Private Network (VPN) is a service that continually changes your IP address to a Secure Server to keep you anonymous when browsing. This change of IP address and device location with.

Graham Cluley
MAY 17, 2024
Nissan North America has revealed that extortionists who demanded a ransom after breaking into its external VPN and disrupted systems last year also stole the social security numbers of over 53,000 staff. Read more in my article on the Hot for Security blog.

Identity IQ
APRIL 22, 2021
If you want to help secure your digital identity, a virtual private network (VPN) is a great tool you can use for added online privacy. In this guide, we discuss VPNs in detail, including how they work, how they protect you and why you should use one when browsing the web. What is a VPN? How does a VPN Work?

Security Affairs
FEBRUARY 1, 2024
Ivanti will update this knowledge base article as more information becomes available.” Mandiant researchers recently discovered new malware employed by a China-linked APT group known as UNC5221 and other threat groups targeting Ivanti Connect Secure VPN and Policy Secure devices. reads the advisory. “Be 20240126.5.xml” 20240126.5.xml”

Trend Micro
AUGUST 30, 2020
The VPN global market only seems to increase as time goes by. What do VPNs provide that make them so attractive? In this article, we share how to choose VPNs and how to secure them.

eSecurity Planet
DECEMBER 23, 2020
Many organizations have used VPNs for years to provide seamless connectivity without compromising security for employees who travel or work remotely. These VPN endpoints are typically set up to support 5 to 10 percent of a company’s workforce at any given time. Enhance VPN Security. Add New VPNs to Support Increased Demand.

Schneier on Security
AUGUST 25, 2021
Vice has an article about how data brokers sell access to the Internet backbone. It’s useful for cybersecurity forensics, but can also be used for things like tracing VPN activity. This is netflow data. At a high level, netflow data creates a picture of traffic flow and volume across a network.

CSO Magazine
APRIL 20, 2021
Over the past few months, several cyberespionage groups, including one believed to be tied to the Chinese government, have been breaking into the networks of organizations from the United States and Europe by exploiting vulnerabilities in VPN appliances from zero-trust access provider Pulse Secure. Sign up for CSO newsletters. ].

Trend Micro
SEPTEMBER 21, 2020
In this entry, we share how threat actors are bundling legitimate Windscribe VPN installers with backdoors. Backdoors allow cybercriminals to gain access and control of computers remotely without the need for proper authentication.

CSO Magazine
OCTOBER 11, 2021
Learn the 5 key tasks to optimize VPNs for security. | To read this article in full, please click here Since then, it has become the norm for large numbers of employees to regularly work from home, with many only going to the office sporadically (if at all). Get the latest from CSO by signing up for our newsletters. ]

Adam Levin
NOVEMBER 26, 2019
Our team was able to access this server because it was completely unsecured and unencrypted,” announced VPN review website vpnMentor in a blog article describing their findings. . The personally identifiable information of children was included in several of the records.

Trend Micro
MARCH 28, 2023
We discovered a new malware, which we named “OpcJacker” (due to its opcode configuration design and its cryptocurrency hijacking ability), that has been distributed in the wild since the second half of 2022.

CSO Magazine
JANUARY 13, 2023
Remote code execution in FortiOS SSL-VPN. The vulnerability, tracked as CVE-2022-42475 , is in the SSL-VPN functionality of FortiOS and can be exploited by remote attackers without authentication. To read this article in full, please click here Successful exploitation can result in the execution of arbitrary code and commands.

GlobalSign
MARCH 27, 2023
In this article, we look take a look at whether zero trust or VPNs are more secure for remote work.

CSO Magazine
MAY 4, 2023
Its transformation overhaul was driven by three reasons: compliance with financial services regulations like PCI DSS, replacing traditional VPN technology to improve user experiences and traffic visibility, and strengthening security controls to its Amazon Web Services (AWS) environment. To read this article in full, please click here
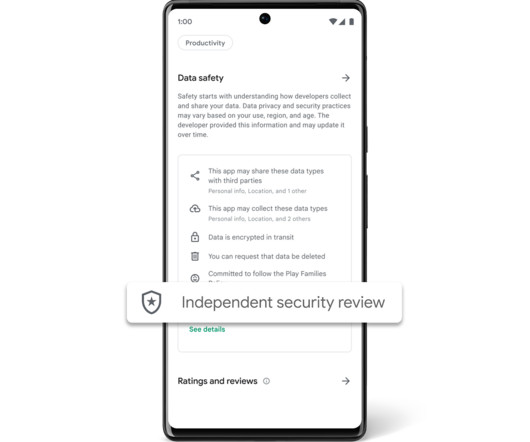
Google Security
NOVEMBER 2, 2023
Highlighting Independently Security Tested VPN Apps Last year, App Defense Alliance (ADA) introduced MASA (Mobile App Security Assessment), which allows developers to have their apps independently validated against a global security standard. We believe the same principles apply for labeling and badging in the Google Play store.

CSO Magazine
JUNE 23, 2021
With the recent Colonial Pipeline attack , the initial infection point was reportedly an old, unused, but still open VPN account. The VPN account did not have two-factor authentication ( 2FA ) enabled, allowing the attacker to merely log in. To read this article in full, please click here (Insider Story)

CSO Magazine
MAY 8, 2023
In the attacks seen so far the attackers gained access by exploiting known vulnerabilities in VPN appliances, moved laterally to other systems, and deployed legitimate remote monitoring and management (RMM) tools to achieve persistence on the network. To read this article in full, please click here

Krebs on Security
DECEMBER 2, 2021
28, other Ubiquiti employees spotted the unusual downloads, which had leveraged internal company credentials and a Surfshark VPN connection to hide the downloader’s true Internet address. The message was sent through an IP address associated with the same Surfshark VPN. When FBI agents raided Sharp’s residence on Mar.

SecureList
APRIL 22, 2024
In our previous article , we described tools for collecting and exfiltrating files ( LoFiSe and PcExter ). Note that all tools described in this article are applied at the stage where the attackers have compromised high-privileged user credentials allowing them to connect to remote hosts.

Schneier on Security
APRIL 7, 2020
If the organization is lucky, they will have already set up a VPN for remote access. Handing people VPN software to install and use with zero training is a recipe for security mistakes, but not using a VPN is even worse. Three, employees are more likely to access their organizational networks insecurely.

CyberSecurity Insiders
MAY 4, 2023
In this article, we will discuss 10 effective ways to protect your privacy online. 3. Use a VPN: A Virtual Private Network (VPN) encrypts your internet traffic, making it difficult for anyone to spy on your online activities. A VPN also allows you to access geo-restricted content and protect your online identity.

CSO Magazine
FEBRUARY 8, 2021
With most companies forced to transition to remote work, even employees far removed from IT are now actively relying on VPN gateways to secure interactions with co-workers, partners, and clients. The US Cybersecurity and Infrastructure Security Agency (CISA) has documented a number of attacks through vulnerabilities in VPN gateways.

Schneier on Security
DECEMBER 4, 2018
There are lots of articles about there telling people how to better secure their computers and online accounts. While I agree with some of it, this article contains some particularly bad advice: 1. I think twice about accessing my online bank account from a pubic Wi-Fi network, and I do use a VPN regularly.
Security Affairs
MAY 12, 2024
Every week the best security articles from Security Affairs are free for you in your email box. A new round of the weekly SecurityAffairs newsletter arrived! Enjoy a new round of the weekly SecurityAffairs newsletter, including the international press.
Security Affairs
JANUARY 13, 2024
Every week the best security articles from Security Affairs are free for you in your email box. A new round of the weekly SecurityAffairs newsletter arrived! Enjoy a new round of the weekly SecurityAffairs newsletter, including the international press.

Krebs on Security
NOVEMBER 2, 2021
.” In the first week of September, Groove posted on its darknet blog nearly 500,000 login credentials for customers of Fortinet VPN products, usernames and passwords that could be used to remotely connect to vulnerable systems. “It’s so funny to read Twitter and the news these days But the result is great so far.

CSO Magazine
OCTOBER 18, 2022
for days, began with attackers using a stolen password to gain access to a legacy VPN system. To read this article in full, please click here In an all-too-familiar pattern, last year’s Colonial Pipeline ransomware attack, which crippled the delivery of fuel supplies to the Southeastern U.S.
CSO Magazine
APRIL 26, 2022
Virtual private network (VPN) provider PureVPN has introduced a quantum-resistant feature to its OpenVPN protocol to provide users with more security and privacy for the post-quantum world. To read this article in full, please click here

Malwarebytes
JANUARY 11, 2024
Successful exploitation would give an attacker the ability to run arbitrary code on Ivanti’s Virtual Private Network (VPN) system. Ivanti Connect Secure is a widely used VPN solution that allows users to connect to their organization’s network. Both are flagging active exploitation of these two chained vulnerabilities.

Security Affairs
JUNE 22, 2023
AnyConnect is a secure remote access VPN (Virtual Private Network) solution developed by Cisco Systems.AnyConnect is widely used by organizations to enable their employees or students to access internal resources and services from remote locations. . The client update process is executed after a successful VPN connection is established.”

Malwarebytes
JANUARY 22, 2023
Article 8 of the Human Rights Act protects your right to respect for your private and family life. You can also tighten your privacy by using a Virtual Private Network (VPN) to anonymize your traffic. In short and easy terms, a VPN acts as a middle-man between a user and the internet.
CSO Magazine
NOVEMBER 5, 2021
In reality, however, many of the DDoS attacks waged against enterprises target components that have long been a part of the network—things such as virtual private network (VPN) devices, firewalls, load balancers and other edge devices. To read this article in full, please click here This makes them susceptible to DDoS attacks.

CSO Magazine
JANUARY 25, 2021
Initially the company suspected that several of its Secure Mobile Access (SMA) series physical and virtual appliances, as well as the NetExtender VPN client and SonicWall firewalls were vulnerable. To read this article in full, please click here However, after further investigation, the list of vulnerable products was revised Saturday.
Malwarebytes
AUGUST 25, 2021
How many free articles have they read. You can also tighten your privacy by using a Virtual Private Network (VPN) to anonymize your traffic. You have options here, since you can install a VPN to anonymize all your Internet traffic, or you can install a VPN extension that will do so for your browser only.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content