Dark web threats and dark market predictions for 2024
SecureList
JANUARY 17, 2024
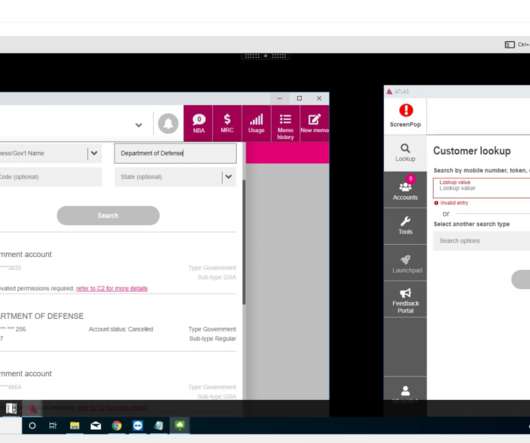
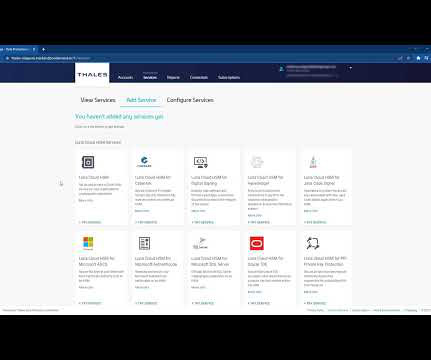
Number of posts offering RedLine logs, 2022–2023 Last year, we released an in-depth study on MaaS, offering detailed insights into the market landscape and the complexity of toolsets used by attackers. The dark market is already replete with such services. Threat actors with a reputation refrained from claiming hacks or posting fakes.






































Let's personalize your content