How to Prevent Phishing Attacks with Multi-Factor Authentication
Tech Republic Security
JANUARY 25, 2024
Learn how to protect yourself and your sensitive information from phishing attacks by implementing multi-factor authentication.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Tech Republic Security
JANUARY 25, 2024
Learn how to protect yourself and your sensitive information from phishing attacks by implementing multi-factor authentication.

Malwarebytes
MAY 16, 2024
More and more websites and services are making multi-factor-authentication (MFA) mandatory, which makes it much harder for cybercriminals to access your accounts. A type of phishing we’re calling authentication-in-the-middle is showing up in online media. That’s a great thing. Use security software.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Security Boulevard
MARCH 15, 2024
In the ever-evolving landscape of cybersecurity, a fresh menace has emerged, targeting crypto enthusiasts through a sophisticated phishing kit. Learning how to avoid crypto phishing is crucial […] The post Crypto Phishing Kit Impersonating Login Pages: Stay Informed appeared first on TuxCare.

Security Boulevard
MARCH 18, 2024
Last week, Microsoft said in an SEC filing that that information stolen in a hack of senior leaders’ email accounts is now being used to “gain or attempt to gain access” to company source code repositories and other internal systems. The post Protecting Against Attacks on NTLM Authentication appeared first on Security Boulevard.
Troy Hunt
AUGUST 30, 2023
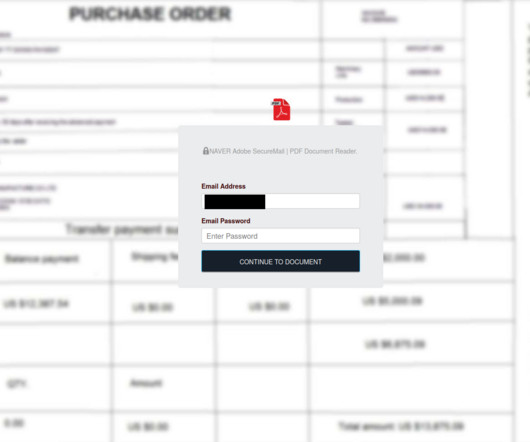
They'd observed a phishing campaign that had collected 68k credentials from unsuspecting victims and asked if HIBP may be used to help alert these individuals to their exposure. Last week I was contacted by CERT Poland. Data accumulated by the malicious activity spanned from October 2022 until just last week.

Malwarebytes
SEPTEMBER 13, 2023
The consequences of last year's LastPass breach continue to be felt, with the latest insult to users coming in the form of a highly convincing phishing email. Armed with this data, attackers can send targeted phishing emails that attempt to steal the passwords needed to unlock the stolen password vaults.
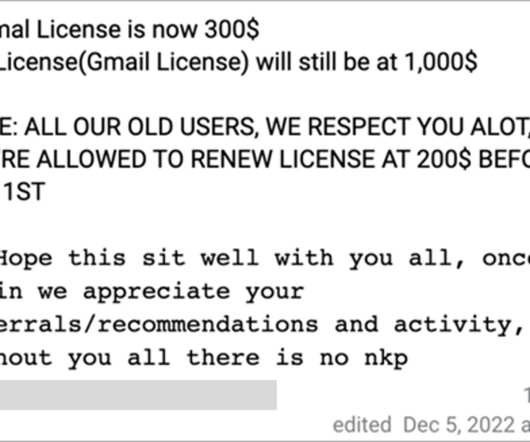
Krebs on Security
APRIL 3, 2024
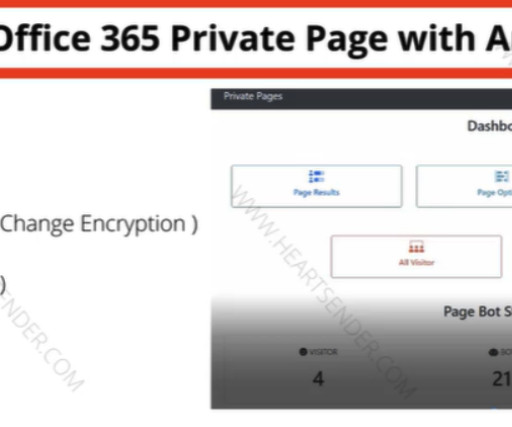
Roughly nine years ago, KrebsOnSecurity profiled a Pakistan-based cybercrime group called “ The Manipulaters ,” a sprawling web hosting network of phishing and spam delivery platforms. Manipulaters advertisement for “Office 365 Private Page with Antibot” phishing kit sold on the domain heartsender,com.

The Last Watchdog
JULY 24, 2023
Accessing vital information to complete day-to-day tasks at our jobs still requires using a password-based system at most companies. Today, bad actors are ruthlessly skilled at cracking passwords – whether through phishing attacks, social engineering, brute force, or buying them on the dark web. Some solutions do this today.
Krebs on Security
AUGUST 17, 2023
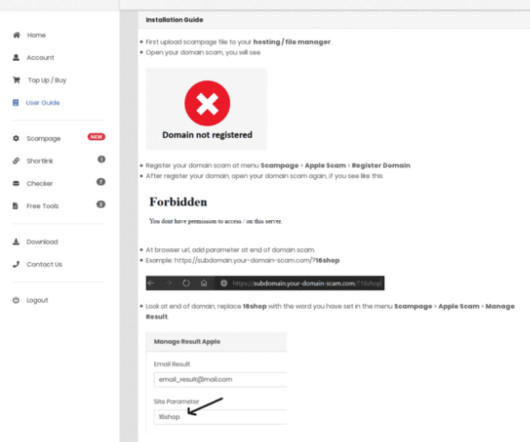
You’ve probably never heard of “ 16Shop ,” but there’s a good chance someone using it has tried to phish you. A 16Shop phishing page spoofing Apple and targeting Japanese users. Image: Akamai.com. The INTERPOL statement says the platform sold hacking tools to compromise more than 70,000 users in 43 countries.

Security Affairs
MAY 13, 2024
Experts reported that since April, the Phorpiex botnet sent millions of phishing emails to spread LockBit Black ransomware. Password Management : Use strong, unique passwords and implement multi-factor authentication (MFA) whenever possible, prioritizing authentication apps or hardware tokens over SMS text-based codes.

Malwarebytes
AUGUST 4, 2023
Attackers believed to have ties to Russia's Foreign Intelligence Service (SVR) are using Microsoft Teams chats as credential theft phishing lures. In the phishing attacks the group leverages previously compromised Microsoft 365 instances, mostly owned by small businesses, to create new domains that look like technical support accounts.

Security Affairs
APRIL 18, 2024
An international law enforcement operation led to the disruption of the prominent phishing-as-a-service platform LabHost. An international law enforcement operation, codenamed Nebulae and coordinated by Europol, led to the disruption of LabHost, which is one of the world’s largest phishing-as-a-service platforms.

Malwarebytes
SEPTEMBER 22, 2023
Some T-Mobile customers logged into their accounts on Wednesday to find another customer’s billing and account information showing on their online dashboards. It said a "temporary system glitch" had misplaced some subscriber account information, causing it to appear on other subscribers’ profile pages. So, stay tuned!
Krebs on Security
FEBRUARY 8, 2021
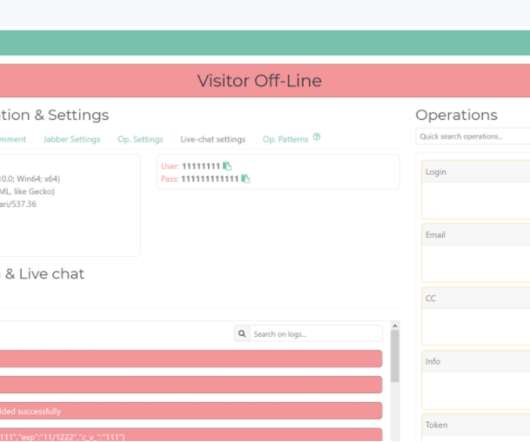
Cyber cops in Ukraine carried out an arrest and several raids last week in connection with the author of a U-Admin , a software package used to administer what’s being called “one of the world’s largest phishing services.” The U-Admin phishing panel interface. Image: fr3d.hk/blog. ” U-Admin, a.k.a.

Joseph Steinberg
JUNE 1, 2021
Cybercriminals Are Impersonating Meal-Kit Services In Order To Steal Money And Personal Information. Cybercriminals know that the more subscribers a service has, the more likely that messages sent to random phone numbers will reach subscribers who believe that the received messages are authentic communications from the relevant service.

Identity IQ
FEBRUARY 8, 2024
How to Spot an Email Phishing Attempt at Work IdentityIQ In the modern workplace, technology is just as common as the typical morning cup of coffee. Among these ever-present threats is phishing, which is a deceptively simple yet effective method cybercriminals use to compromise both business and personal accounts. What Is Phishing?

Schneier on Security
DECEMBER 14, 2018
Attackers are targeting two-factor authentication systems: Attackers working on behalf of the Iranian government collected detailed information on targets and used that knowledge to write spear-phishing emails that were tailored to the targets' level of operational security, researchers with security firm Certfa Lab said in a blog post.

Identity IQ
FEBRUARY 7, 2023
What is Phishing? They learn new security measures quickly and find new ways to steal sensitive information. One of the most common techniques used to exploit web users is the phishing scam. This article will cover what phishing is, cybercriminals’ different approaches, and how to prevent yourself from becoming a victim.

SecureWorld News
FEBRUARY 15, 2024
A sophisticated form of mobile malware dubbed "GoldPickaxe" has been uncovered, which collects facial recognition data to produce deepfake videos, enabling hackers to bypass biometric authentication protections on banking apps. Experts warn that biometric authentication alone is not foolproof.

eSecurity Planet
AUGUST 23, 2023
Spear phishing is a more targeted and effective phishing technique that attempts to exploit specific individuals or groups within an organization. While phishing uses a broader range of tactics, such as mass emailing to random recipients, spear phishing is often well-researched and tailored to high-value targets.
Security Affairs
OCTOBER 12, 2023
This post analyzed the numerous phishing campaigns targeting users and organizations in Italy. Phishing is a ploy to trick users into revealing personal or financial information through an e-mail, Web site, and even through instant messaging. Phishing can also be used as a precursor attack to drop malware.
Security Affairs
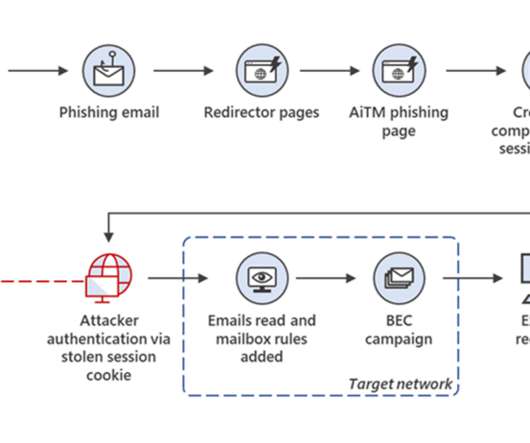
JULY 12, 2022
A large-scale phishing campaign used adversary-in-the-middle (AiTM) phishing sites to hit more than 10,000 organizations. In AiTM phishing, threat actors set up a proxy server between a target user and the website the user wishes to visit, which is the phishing site under the control of the attackers.

SecureList
APRIL 5, 2023
They have become adept at using Telegram both for automating their activities and for providing various services — from selling phishing kits to helping with setting up custom phishing campaigns — to all willing to pay. ” Links to the channels are spread via YouTube, GitHub and phishing kits they make.

Identity IQ
FEBRUARY 14, 2024
What Is Spear Phishing and How to Avoid It IdentityIQ Have you ever clicked a suspicious link or opened an unexpected attachment, only to realize it was a scam? The internet, brimming with information and opportunity, can also be dangerous. That’s where spear phishing comes in – a particularly cunning form of online deception.

The Last Watchdog
NOVEMBER 29, 2022
A new development in phishing is the “nag attack.” The end game, of course, is to trick an intended victim into revealing sensitive information or it could be to install malicious code. Nag attacks add to the litany of phishing techniques. Over the years, endless phishing variants have emerged, including: •Bulk phishing.
Security Affairs
MARCH 14, 2023
Microsoft warns of large-scale phishing attacks orchestrated with an open-source adversary-in-the-middle (AiTM) phishing kit available in the cybercrime ecosystem Adversary-in-the-middle (AiTM) phishing kits are becoming an essential technology in the cybercrime ecosystem that is used by multiple threat actors to launch phishing attacks.

Thales Cloud Protection & Licensing
OCTOBER 4, 2022
Cybersecurity Awareness Month: Resilient Multi-factor Authentication (MFA) and Strong Passwords. Recognize and report phishing. Most of the impact is fraudulent financial and personal information use and tailored scams based on their information. Resilient multi-factor authentication and strong passwords are critical.
SecureList
AUGUST 14, 2023
Examples include automation with phishing kits or Telegram bots. Besides tucking a phishing page inside the website they hack, scammers can steal all of the data on the server and completely disrupt the site’s operation. The rest of this article will deal with phishing pages on hacked websites that are powered by WordPress.

Identity IQ
AUGUST 21, 2023
What is Clone Phishing and How Do I Avoid It? One of the most devious tricks that they use is called clone phishing. In this blog post, we dive into the world of clone phishing, shedding light on what it is, the potential risks it poses, and most importantly, how to protect yourself from falling victim to it.

Security Boulevard
AUGUST 21, 2021
The post DEF CON 29 Main Stage – Jenko Hwong’s ‘New Phishing Attacks Exploiting OAuth Authentication Flows’ appeared first on Security Boulevard. Our thanks to DEFCON for publishing their outstanding DEFCON Conference Main Stage Videos on the groups' YouTube channel.
Identity IQ
AUGUST 31, 2023
How to Identify and Avoid Holiday Phishing Scams IdentityIQ The holiday season brings joy, celebrations, and… a surge in online scams. While you’re shopping for gifts or booking flights, hackers are plotting to trick you into revealing your personal details and financial information. What Is a Phishing Scam? Their goal?

Malwarebytes
APRIL 18, 2024
A major international law enforcement effort involving agencies from 19 countries has disrupted the notorious LabHost phishing-as-a-service platform. This data will be used to support ongoing international operational activities focused on targeting the malicious users of this phishing platform.

Adam Levin
MARCH 23, 2020
As more employees are working remotely in the wake of the Covid-19 pandemic, businesses are being targeted by an increasing number of phishing campaigns. . Avoid sending sensitive information like tax forms, credit card numbers, bank account information, or passwords via email. The post Working Remotely?
eSecurity Planet
AUGUST 19, 2022
One new tactic hackers have been using is to steal cookies from current or recent web sessions to bypass multi-factor authentication (MFA). Even cloud infrastructures rely on cookies to authenticate their users. Browsers allow users to maintain authentication, remember passwords and autofill forms. How Hackers Steal Cookies.

Daniel Miessler
MARCH 10, 2022
People are starting to get the fact that texts (SMS) are a weak form of multi-factor authentication (MFA). The answer is remarkably simple, actually— phishing. This means traditional MFA is becoming increasingly useless against phishing in the real world. It completely changes how authentication is done.
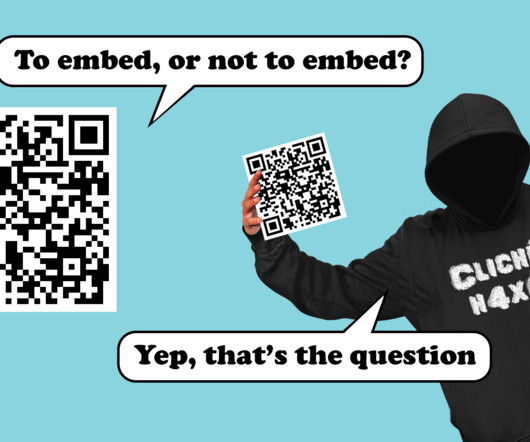
Pen Test Partners
FEBRUARY 14, 2024
October 2023’s Cyber Security Awareness Month led to a flurry of blog posts about a new attack called Quishing (QR Code phishing) and how new AI powered email gateways can potentially block these attacks. Currently, most initial access attempts are carried out with social engineering, commonly phishing. What’s the attack?
SecureWorld News
JUNE 6, 2023
In our most recent Remote Sessions webcast, Roger Grimes, computer security expert and Data-Driven Defense Evangelist for KnowBe4, gave a deep dive on phishing and how to properly mitigate and prevent phishing attacks. What is phishing? Also known as spamming, phishing is typically done through email, SMS, and phone attacks.

SC Magazine
JULY 2, 2021
Researchers reported on Friday that cybercriminals are mimicking legitimate correspondence to actively target popular cloud applications DocuSign and SharePoint in phishing attacks designed to steal user log-in credentials. The post Phishing attack targets DocuSign and SharePoint users appeared first on SC Media.

SecureBlitz
DECEMBER 15, 2021
This post will show you how to fight phishing with security intelligence. Phishing is one of the most frequent cyberattacks that trick users into revealing their personal information to an unreliable source – the hacker.
Krebs on Security
JANUARY 7, 2020
Late last year saw the re-emergence of a nasty phishing tactic that allows the attacker to gain full access to a user’s data stored in the cloud without actually stealing the account password. The phishing lure starts with a link that leads to the real login page for a cloud email and/or file storage service. Image: Phishlabs.

SecureWorld News
AUGUST 28, 2023
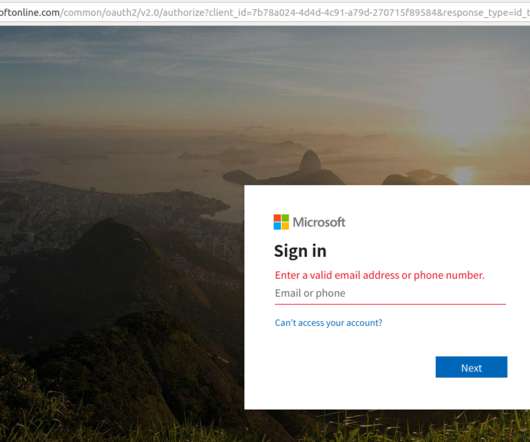
In May 2023, a phishing campaign was launched that targeted a major U.S. The emails in the campaign purported to be from Microsoft, and they claimed that the recipient needed to update their account security settings or activate two-factor authentication (2FA)/multi-factor authentication (MFA) within 72 hours.
Security Affairs
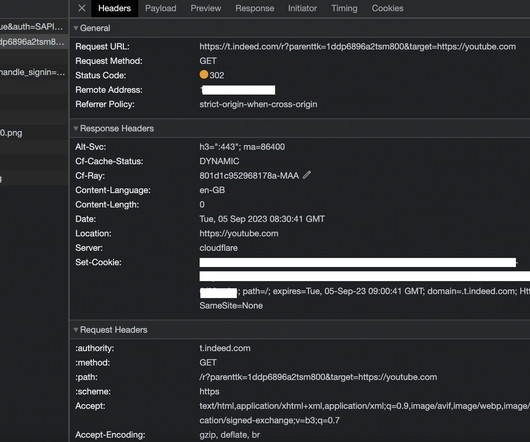
OCTOBER 4, 2023
Threat actors exploited an open redirection vulnerability in the job search platform Indeed to carry out phishing attacks. Researchers from the cybersecurity firm Menlo Security reported that threat actors exploited an open redirection vulnerability in the job search platform Indeed in phishing attacks. ” continues the report.
Security Affairs
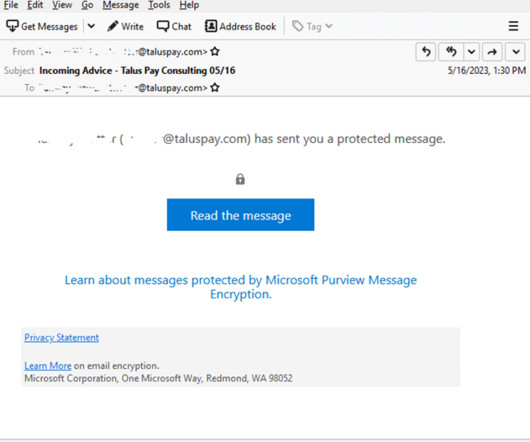
MAY 29, 2023
Experts warn of phishing attacks that are combining the use of compromised Microsoft 365 accounts and.rpmsg encrypted emails. Trustwave researchers have observed threat actors using encrypted RPMSG attachments sent via compromised Microsoft 365 accounts in a phishing campaign aimed at stealing Microsoft credentials.

Duo's Security Blog
APRIL 20, 2023
Through the first two months of 2023 alone, the Australian Competition and Consumer Commission’s Scamwatch reported more than 19,000 phishing reports with estimated financial losses of more than $5.2 What is phishing? This is part of what makes phishing attacks so dangerous.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content