Email Security Guide: Protecting Your Organization from Cyber Threats
CyberSecurity Insiders
APRIL 16, 2023
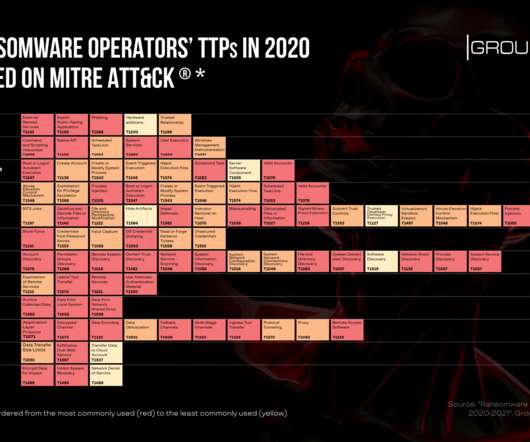
Latest email security trends Phishing and spear-phishing attacks: Phishing is a type of social engineering attack where cybercriminals use deceptive emails to trick recipients into divulging sensitive information or downloading malware.
















































Let's personalize your content