GUEST ESSAY: A roadmap for wisely tightening cybersecurity in the modern workplace
The Last Watchdog
MAY 24, 2023
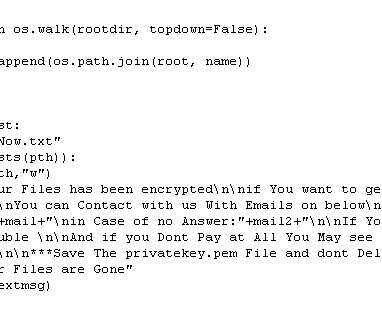
Related: Tapping hidden pools of security talent Sometimes hackers can encrypt your systems, holding them hostage and asking you to pay money to regain access to them. This problem, called ransomware , explains why keeping backups is so important. Cyberattacks can also lead to a loss of productivity.













































Let's personalize your content