A Reactive Cybersecurity Strategy Is No Strategy at All
CyberSecurity Insiders
MAY 18, 2022
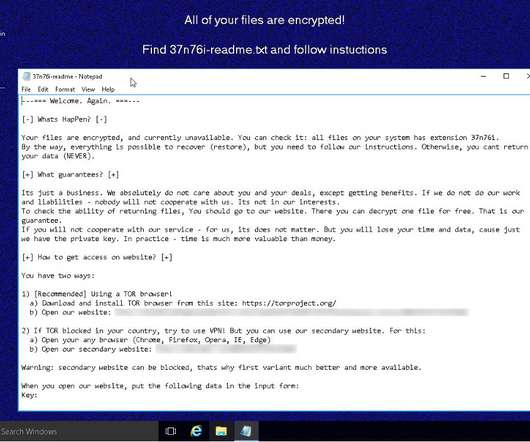
But what are your options for proactive protection when the notion of a walled-in network has been shattered by the proliferation of new IoT devices, growth of cloud services, and new hybrid work from home models? When malware first breaches a network, it doesn’t make its presence known right away. So where do we go from here?





















Let's personalize your content