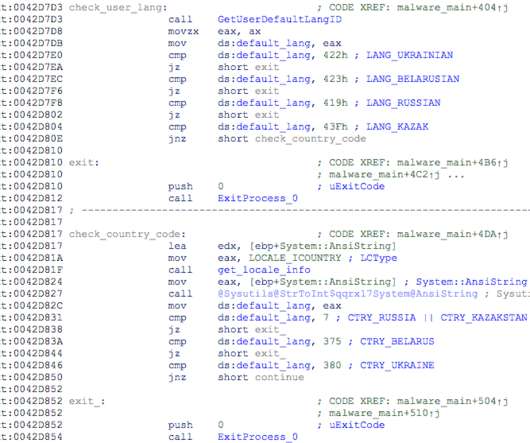
Ransomware attack on MSI led to compromised Intel Boot Guard private keys
Malwarebytes
MAY 8, 2023
While the statement does not reveal a lot of tangible information, this snippet is important: “MSI urges users to obtain firmware/BIOS updates only from its official website, and not to use files from sources other than the official website.” Stop malicious encryption. Create offsite, offline backups.



































Let's personalize your content