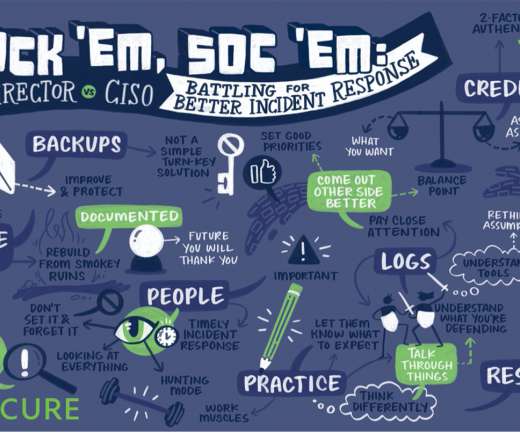
Recapping Cisco Secure at Black Hat USA 2021
Cisco Security
AUGUST 11, 2021
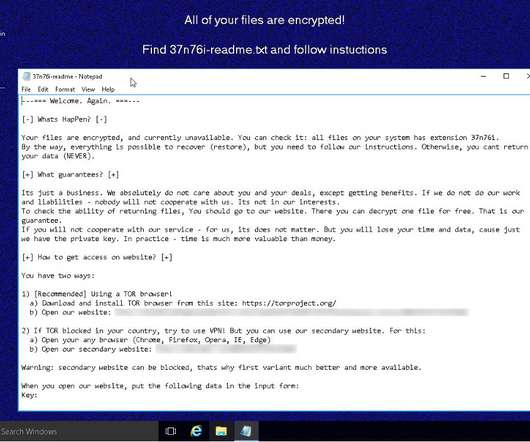
Backups… Let’s Get This Out of the Way. A challenge with outsourcing backup responsibilities is that companies often have no say in how often or the level at which third parties back up their information. “With ransomware being as big as it is right now, one of the first answers that everyone goes to is backups.”























Let's personalize your content