News alert: INE Security shares cyber hygiene guidance for small- and medium-sized businesses
The Last Watchdog
OCTOBER 23, 2024
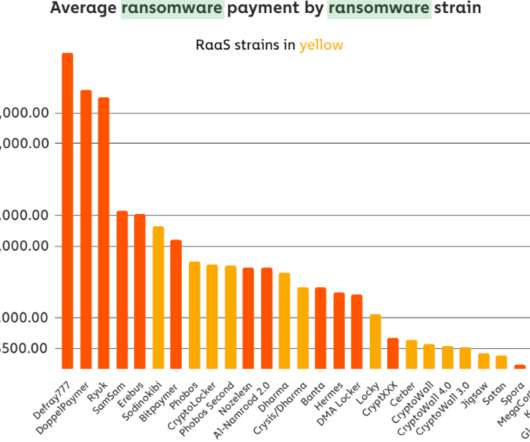
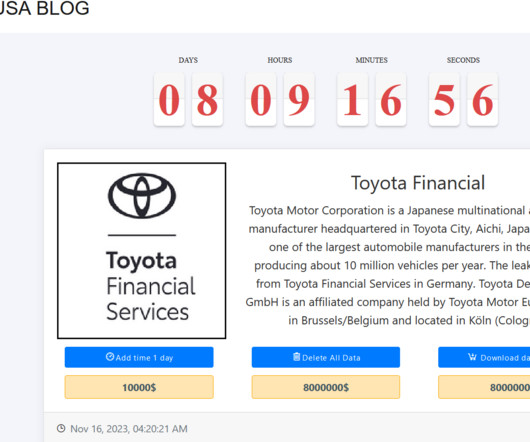
As small businesses increasingly depend on digital technologies to operate and grow, the risks associated with cyber threats also escalate. Regular backups ensure that businesses can recover quickly from ransomware attacks or other data loss incidents. Cary, NC, Oct. 1 – Storing 1 copy offsite (e.g.,













































Let's personalize your content