CISOs in Australia Urged to Take a Closer Look at Data Breach Risks
Tech Republic Security
MAY 24, 2024
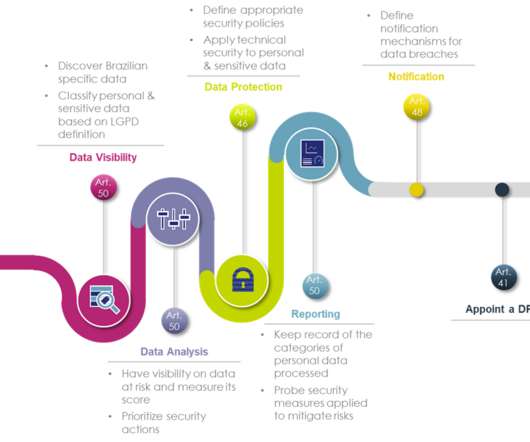
A leading cyber lawyer in Australia has warned CISOs and other IT leaders their organisations and careers could be at stake if they do not understand data risk and data governance practices.





































Let's personalize your content