Tackling Cyber Threats: Is AI Cybersecurity Our Only Hope?
Jane Frankland
MAY 8, 2024
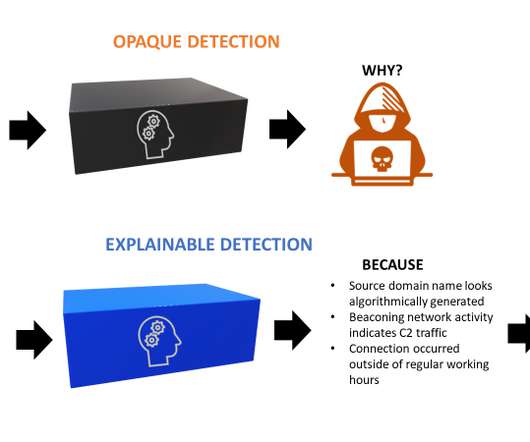
Could artificial intelligence (AI) be the key to outsmarting cyber threats in an increasingly connected world? On one hand, AI has been hailed as a game-changing technology with the potential to transform industries and improve our daily lives. As CISOs, and ITDMs who are responsible for cybersecurity we can do three things: 1.
































Let's personalize your content