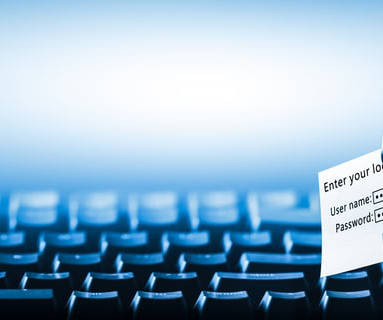
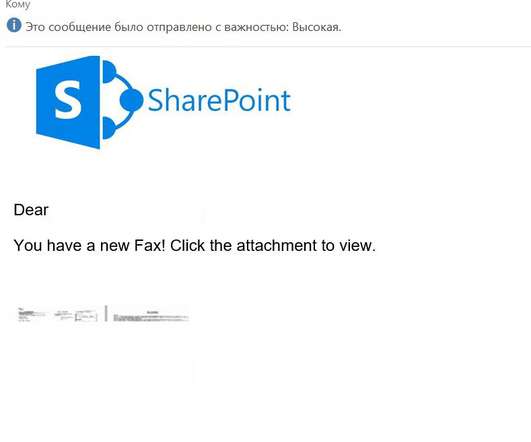
Concession in Social Engineering
Security Through Education
APRIL 23, 2024
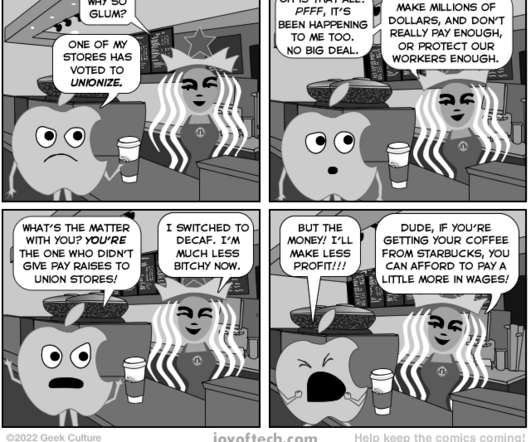
Unknowingly, you have just succumbed to a technique we in social engineering refer to as “ concession.” What are ways we can be more aware of concession being used against us? Now imagine how powerful this would be when leveraged maliciously by a professional social engineer! “Oh, I can’t afford that!”








































Let's personalize your content