Facing the New Security Challenges That Come With Cloud
Dark Reading
AUGUST 22, 2022
Organizations relying on multicloud or hybrid-cloud environments without ?a a true understanding of their security vulnerabilities do so at their peril.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 cloud-security facing-the-new-security-challenges-that-come-with-cloud
cloud-security facing-the-new-security-challenges-that-come-with-cloud 
Dark Reading
AUGUST 22, 2022
Organizations relying on multicloud or hybrid-cloud environments without ?a a true understanding of their security vulnerabilities do so at their peril.

The Last Watchdog
MAY 16, 2024
Meeting the demands of the modern-day SMB is one of the challenges facing many business leaders and IT operators today. Thankfully, with the advent of cloud offerings, a new scalable model has entered the landscape; whether it be 20 or 20,000 users, the cloud will fit all and with it comes a much simpler, per user cost model.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

The Last Watchdog
JANUARY 2, 2024
In today’s digital landscape, organizations face numerous challenges when it comes to mitigating cyber risks. Related: How AI is transforming DevOps The constant evolution of technology, increased connectivity, and sophisticated cyber threats pose significant challenges to organizations of all sizes and industries.

The Last Watchdog
DECEMBER 14, 2023
Their guidance: Brandon Colley , Principal Security Consultant, Trimarc Security Colley Some 10-year-old vulnerabilities are still wildly prevalent. Their guidance: Brandon Colley , Principal Security Consultant, Trimarc Security Colley Some 10-year-old vulnerabilities are still wildly prevalent.

Thales Cloud Protection & Licensing
MARCH 24, 2024
Data Security Trends: 2024 Report Analysis madhav Mon, 03/25/2024 - 05:08 Amid ongoing economic uncertainty and a progressively complex threat landscape, businesses are trying to navigate increasingly stringent regulatory requirements while bolstering their security posture.

The Last Watchdog
JUNE 6, 2022
Related: Why security teams ought to embrace complexity. As RSA Conference 2022 gets underway today in San Francisco, advanced systems to help companies comprehensively inventory their cyber assets for enhanced visibility to improve asset and cloud configurations and close security gaps will be in the spotlight.

The Last Watchdog
DECEMBER 14, 2023
Here’s the final installment of leading technologists sharing their observations about cybersecurity developments in the year that’s coming to a close — and the year to come. Consumers will begin to see their favorite applications touting “quantum-secure encryption.” Their guidance: Snehal Antani , CEO, Horizon3.ai

Security Affairs
APRIL 10, 2024
As technology evolves and our dependence on digital systems increases, the cybersecurity threat landscape also rapidly changes, posing fresh challenges for organizations striving to protect their assets and data. The common maxim today is that when it comes to breaches, it’s no longer a case of ‘if’ but ‘when’ or ‘how often?’.

CyberSecurity Insiders
DECEMBER 21, 2022
With continued challenges from remote and hybrid working, increased economic unrest and geopolitical conflict, and a new gang of teenage hackers , 2022 has certainly thrown cybersecurity professionals some curveballs. Here are a few trends to watch out for in the new year: Cyber threats emerge as a result of hybrid working.

The Last Watchdog
MAY 17, 2021
A greater good has come from Capital One’s public pillaging over losing credit application records for 100 million bank customers. In pulling off that milestone hack, Paige Thompson took advantage of CapOne’s lack of focus on cloud security as the banking giant rushed headlong into leveraging Amazon Web Services.

CyberSecurity Insiders
JANUARY 17, 2022
Knowing When to Move Threat Detection, Investigation and Response (TDIR) to the Cloud. While organizations faced an unknown road ahead, they were quick to adapt. In the face of challenges never seen before, businesses have evolved, many having changed radically since the beginning of last year.
Thales Cloud Protection & Licensing
DECEMBER 6, 2023
Securing the Cloud Frontier: Navigating the Complexities of SaaS Data Protection in the Multi-Cloud Era madhav Thu, 12/07/2023 - 05:34 In the rapidly evolving digital landscape, Software as a Service (SaaS) has emerged as a cornerstone of modern business operations. cloud platforms and 97 SaaS applications.

The Last Watchdog
APRIL 29, 2020
It can be argued that we live in a cloud-mobile business environment. Related: The ‘shared responsibility’ burden Most organizations are all caught up, to one degree or another, in migrating to hybrid cloud networks. And startups today typically launch with cloud-native IT infrastructure.
Thales Cloud Protection & Licensing
SEPTEMBER 11, 2023
Thales 2023 Data Threat Report: The Increased Telco Cybersecurity Challenges in the 5G Era madhav Tue, 09/12/2023 - 05:15 Telecommunications firms have always faced a unique set of security challenges. According to the GSMA, the world’s telcos will spend around $1 trillion on 5G launches.

The Last Watchdog
MAY 23, 2022
Digital services get delivered across a complex amalgam of public cloud, hybrid cloud and on-premises digital systems. And yet at this moment, digital trust isn’t where it needs to be on the boardroom priority list or the IT security team’s strategy. This challenge has not escaped the global cybersecurity community.
CyberSecurity Insiders
MAY 2, 2023
By Dan Benjamin, Co-Founder and CEO, Dig Security Approximately 60% of corporate data now lives in the cloud, a number that has doubled over the last seven years. While the concept of cloud computing dates back decades, it is only in the past few years that organizations have begun to understand its full potential.

NetSpi Executives
DECEMBER 19, 2023
It’s a question older than the internet—do we optimize our existing tech stack or invest in new technology? The debate is as fresh today as ever, especially with the saturation of solutions promising to simplify security stacks. In your experience, what are the top challenges SOC teams face with detection and response controls?

eSecurity Planet
JANUARY 18, 2024
Cloud storage is a cloud computing model that allows data storage on remote servers operated by a service provider, accessible via internet connections. It excels in remote access, scalability, and security, with distributed storage options and privacy adherence capabilities.

Thales Cloud Protection & Licensing
SEPTEMBER 13, 2021
Authentication and access management increasingly perceived as core to Zero Trust Security. While many consider that remote access to corporate resources and data as the key disruption, security teams had to face many more challenges. Tue, 09/14/2021 - 05:52. State of Multi-Factor Authentication.

eSecurity Planet
JANUARY 30, 2024
Cloud storage security issues refer to the operational and functional challenges that organizations and consumers encounter when storing data in the cloud. Cloud storage risks involve potential external threats and vulnerabilities that jeopardize the security of stored data.

The Last Watchdog
MARCH 11, 2020
Organizations are increasingly outsourcing IT workloads to cloud service providers and looking to leverage IoT systems. A big challenge security executives face is balancing speed vs. security. Cyber hygiene basics revolve around aligning people, processes and technologies to adopt a security-first mindset.

CyberSecurity Insiders
OCTOBER 14, 2021
As employees increasingly worked remotely during the pandemic, businesses quickened their pace toward the cloud. Already, the need for application agility was driving cloud adoption. As such, according to Radware’s The State of Web Application and API Protection report, 70% of production web applications now run in cloud environments.

eSecurity Planet
DECEMBER 19, 2023
Attack surfaces will explode: Cyberdefense complexity will compound as API, cloud, edge, and OT resources add to the list of assets to defend. ” “AI-related innovations will create new possibilities we’re not even considering at the moment,” cautions Manny Rivelo, CEO of Forcepoint.

Security Affairs
FEBRUARY 8, 2024
26 key cyber security stats for 2024 that every user should know, from rising cyber crime rates to the impact of AI technolog y. Shockingly, 96% of these attacks come through email. Shockingly, 96% of these attacks come through email. of organizations faced ransomware. Ransomware Attacks: In 2023, a whopping 72.7%

CyberSecurity Insiders
APRIL 20, 2023
By Mishel Mejibovski, Head of Operations and Strategy, SURF Security While some companies insist on going back to their original work practices and are forcing their employees back into the office, many others have realized the benefits of hybrid work models and have adopted them as their new way of operations.

Centraleyes
FEBRUARY 25, 2024
In the digital era, cloud computing has become synonymous with agility and scalability for businesses and individuals. However, critical security risks and threats inherent in cloud environments come alongside the myriad benefits. Who’s Responsible for Security in the Cloud?
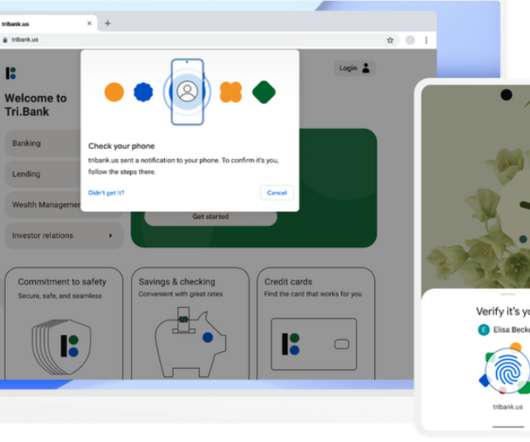
Krebs on Security
MAY 7, 2022
According to the FIDO Alliance, users will be able to sign in to websites through the same action that they take multiple times each day to unlock their devices — including a device PIN, or a biometric such as a fingerprint or face scan. Image: Blog.google.

Krebs on Security
AUGUST 2, 2019
But new information indicates the methods she deployed have been well understood for years. What follows is based on interviews with almost a dozen security experts, including one who is privy to details about the ongoing breach investigation.

Anton on Security
AUGUST 30, 2021
As you are reading our recent paper “Autonomic Security Operations?—?10X 10X Transformation of the Security Operations Center” , some of you may think “Hey, marketing inserted that 10X thing in there.” Attackers come, alerts trigger, we clear them, adjust, tune, response, rinse, repeat. Does this remind you of SOC analyst work?

Thales Cloud Protection & Licensing
APRIL 3, 2024
In the financial industry, this effect has been accentuated by rapid digital transformation, which has seen a huge number of new players enter the financial ecosystem. In the financial industry, this effect has been accentuated by rapid digital transformation, which has seen a huge number of new players enter the financial ecosystem.

Adam Levin
MARCH 26, 2020
The more you can do to safeguard your company against cyberattacks and employee error, the better you will fare in the coming years. But for those who get in front of the issues facing companies today, it will be a buyer’s market for a long time to come. The cloud continues to be a challenge for companies.
Pen Test
OCTOBER 24, 2023
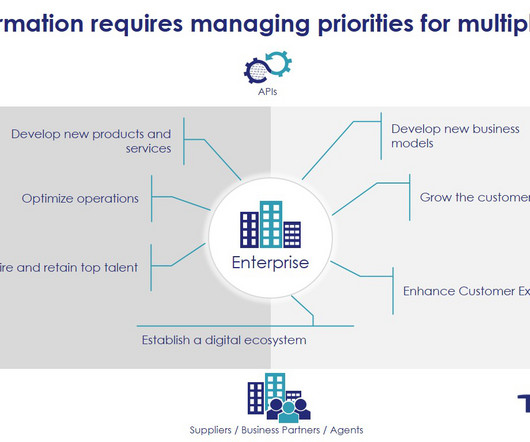
Nowadays, with the evolution of technology, many companies are starting their journey as a cloud native company. All of this information brings us to another important challenge. A cloud strategy is a concise viewpoint on the role of cloud computing in the organization. Let's talk about all of them.

eSecurity Planet
DECEMBER 20, 2023
Attack surface management (ASM) is a relatively new cybersecurity technology that combines elements of vulnerability management and asset discovery with the automation capabilities of breach and attack simulation (BAS) and applies them to an organization’s entire IT environment, from networks to the cloud.

Anton on Security
JULY 20, 2022
Let’s continue our fun conversation on threat detection in the cloud that we started in “Who Does What In Cloud Threat Detection?” and “How to Think about Threat Detection in the Cloud” and continued somewhat in “Detection as Code? and “Does the World Need Cloud Detection and Response (CDR)?” No, Detection as COOKING!”

Security Boulevard
MARCH 24, 2024
Data Security Trends: 2024 Report Analysis madhav Mon, 03/25/2024 - 05:08 Amid ongoing economic uncertainty and a progressively complex threat landscape, businesses are trying to navigate increasingly stringent regulatory requirements while bolstering their security posture.

The Last Watchdog
NOVEMBER 30, 2021
Indeed, APIs have opened new horizons of cloud services, mobile computing and IoT infrastructure, with much more to come. Yet, in bringing us here, APIs have also spawned a vast new tier of security holes. Yet, API security risks haven’t gotten the attention they deserve.

Cisco Security
APRIL 6, 2022
Security has never been more top of mind. Perhaps it’s exacerbated by what’s going on in Ukraine and the challenges it presents to the world, including the real fears over cyberwarfare. Of course, threats becoming advanced, the move to the cloud, and hybrid work remain among our customers’ biggest challenges.

CyberSecurity Insiders
JANUARY 30, 2023
IT departments and data teams are looking at the best ways to prioritize, maintain and build security measures – while being cost effective. It’s a tricky balance to strike but an important one as security cannot be overlooked. How will this happen and how will it impact the data security industry?

The Last Watchdog
APRIL 21, 2021
Related: Why it’s vital to secure IoT. The devil truly is in the details when it comes to how companies are hustling to leverage cloud infrastructure and spin up cool new apps. The devil truly is in the details when it comes to how companies are hustling to leverage cloud infrastructure and spin up cool new apps.

Cisco Security
DECEMBER 2, 2021
It’s yet another way that we are fulfilling our vision to simplify security for networks, workloads, and applications across your multi-cloud world. . Snort is widely used, in several of our own products including Cisco Secure Firewall, Cisco Umbrella, Meraki MX, and used by other industry partners. The Challenge .
Thales Cloud Protection & Licensing
APRIL 11, 2023
New domains like CIEM (Cloud Infrastructure Entitlement Management) and ITDR (Identity Thread Detection and Response) are gaining traction. Cloud-based Access Management Steps Up! madhav Wed, 04/12/2023 - 06:11 Identity and Access Management (IAM) has evolved significantly over the past decade. Is this all coincidental?

CyberSecurity Insiders
NOVEMBER 15, 2021
These unrealistic expectations are the obstacles many cybersecurity professionals face once they complete their studies and rigorous exams. These unrealistic expectations are the obstacles many cybersecurity professionals face once they complete their studies and rigorous exams. You’ve seen the job posting. Be specific.

Anton on Security
FEBRUARY 12, 2024
This hurts properly parsing out relevant pieces of new relevant intel that should go further down the pipeline — focus on a few relevant related news article, on a single report of small series of report, and dedicate at least half a day to fully integrate all the new input before calling shots of what should be pushed further down the process.

The Last Watchdog
MARCH 19, 2020
WhiteHat Security got its start some 17 years ago in Silicon Valley to help companies defend their public-facing websites from SQL injection and cross-site scripting hacks. Yet organizations have many more application security headaches to resolve these days. Office of Personnel Management are two prime examples.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content