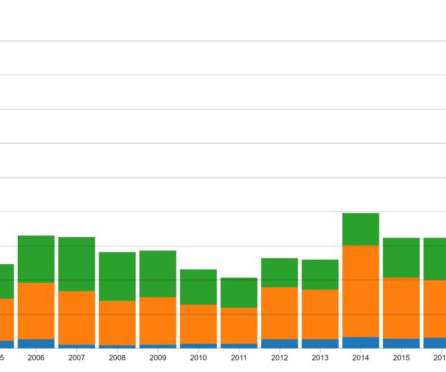
Cyberthreats to financial organizations in 2022
SecureList
NOVEMBER 23, 2021
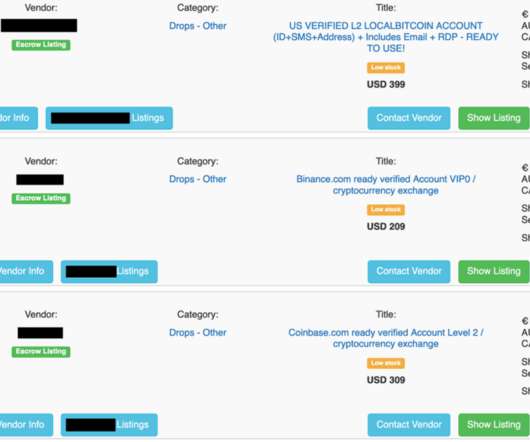
We should expect more fraud, targeting mostly BTC , because this cryptocurrency is the most popular. In fact, from January through the end of October, Kaspersky detected more than 2,300 fraudulent global resources aimed at 85,000 potential crypto investors or users who are interested in cryptocurrency mining.























Let's personalize your content