Satacom delivers browser extension that steals cryptocurrency
SecureList
JUNE 5, 2023
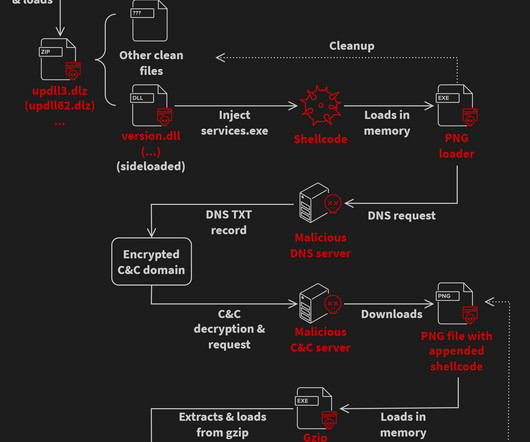
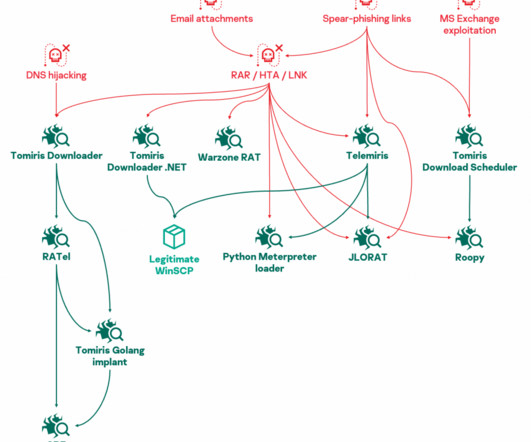
It is known to use the technique of querying DNS servers to obtain the base64-encoded URL in order to receive the next stage of another malware family currently distributed by Satacom. The encrypted data is stored inside the malicious payload. To do so, it performs a DNS request to don-dns[.]com



























Let's personalize your content