North Korean Hackers Steal $1.5B in Cryptocurrency
Schneier on Security
FEBRUARY 25, 2025
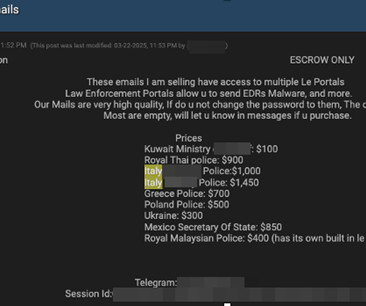
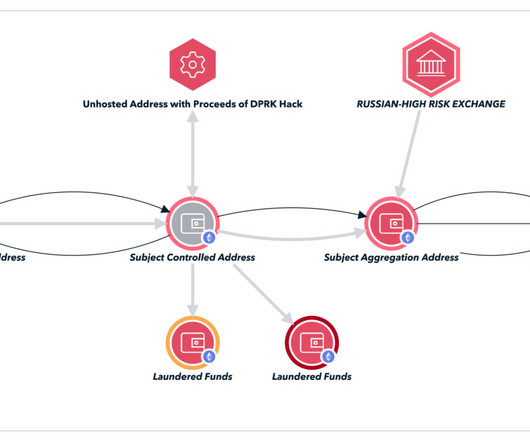
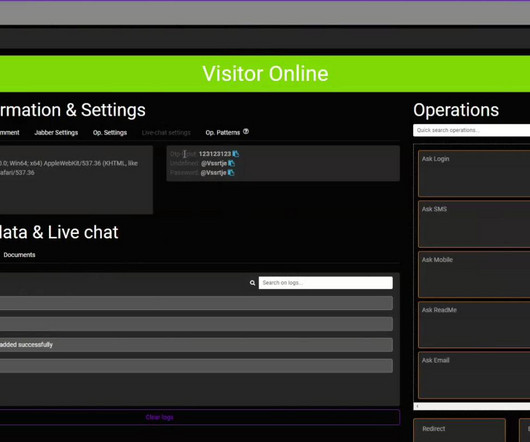
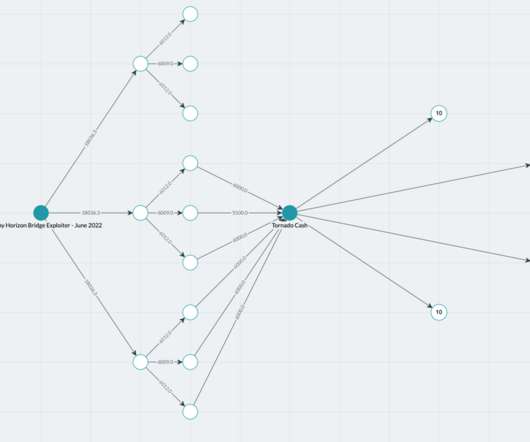
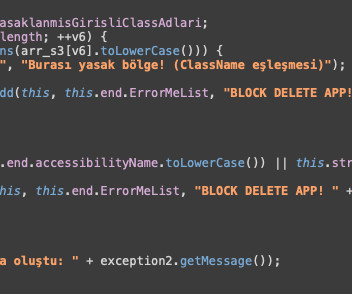
From there, the cryptocurrency was transferred out of Bybit altogether and into wallets controlled by the unknown attackers. […] …a subsequent investigation by Safe found no signs of unauthorized access to its infrastructure, no compromises of other Safe wallets, and no obvious vulnerabilities in the Safe codebase. .”


































Let's personalize your content