Cybersecurity awareness: Train your employees and reduce cyber threats
IT Security Guru
DECEMBER 1, 2022
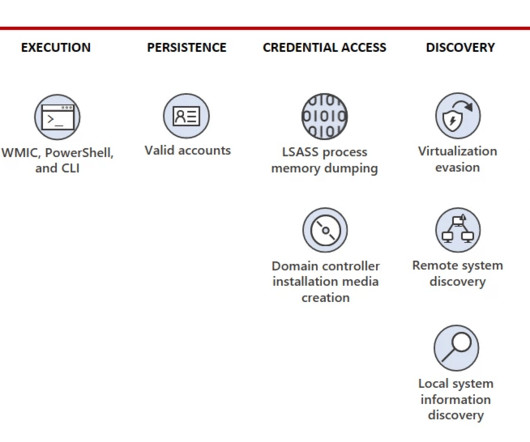
As our digital world evolves, cybersecurity has never been more important and critical. As cybercrime continues to increase, the human element can play the most important role in cybersecurity posture and hygiene. After all, cybersecurity is a matter of proper human risk management. Armed Forces are an exemplary example.
















































Let's personalize your content