Mastering NIST Penetration Testing: Your Essential Guide to Robust Cybersecurity
Security Boulevard
NOVEMBER 28, 2023
Organizations face an ongoing battle against cyber threats; penetration testing is a powerful weapon to avoid these risks.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Security Boulevard
NOVEMBER 28, 2023
Organizations face an ongoing battle against cyber threats; penetration testing is a powerful weapon to avoid these risks.

eSecurity Planet
MARCH 7, 2023
Penetration tests are simulated cyber attacks executed by white hat hackers on systems and networks. There are different types of penetration tests, methodologies and best practices that need to be followed for optimal results, and we’ll cover those here. However, they are also the most realistic tests.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Security Boulevard
MAY 18, 2023
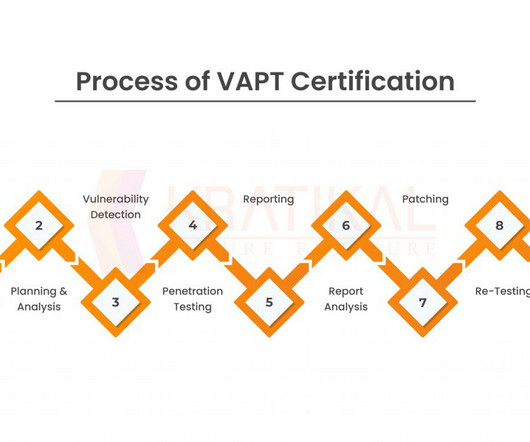
Introduction Making sure our internet systems and data are secure has become crucial in today’s digital world, as technology is ingrained in every part of our lives. Organizations of all sizes are frequently vulnerable to a variety of cyber dangers.

Penetration Testing
DECEMBER 5, 2023
As the digital landscape evolves, so does the nature of cyber threats. 2023 witnessed a significant shift in the tactics and approaches of cyber attackers, influenced by global conflicts and advancements in technology.
NetSpi Executives
SEPTEMBER 26, 2023
At Black Hat, NetSPI VP of Research Karl Fosaaen sat down with the host of the Cloud Security Podcast Ashish Rajan to discuss all things Azure penetration testing. In an era of constantly evolving technology and escalating cyber threats, voices like Karl’s become the bedrock of resilience for today’s cloud security.

The Last Watchdog
OCTOBER 5, 2023
Acohido to share his ideas about the current cyber threat landscape, the biggest threats for businesses today, the role of AI and machine learning in cyberattacks and cyberdefence, and the most effective methods for companies to protect themselves. Erin: What cybersecurity technologies are you most excited about right now?

CyberSecurity Insiders
MAY 3, 2023
Penetration testing (pentesting) is one of the fundamental mechanisms in this area. The following considerations will give you the big picture in terms of prerequisites for mounting a simulated cyber incursion that yields positive security dividends rather than being a waste of time and resources.

The Last Watchdog
MAY 8, 2024
May 8, 2024, CyberNewsWire — Security Risk Advisors (SRA) announces the launch of their OT/XIoT Detection Selection Workshop, a complimentary offering designed to assist organizations in selecting the most suitable operational technology (OT) and Extended Internet of Things (XIoT) security tools for their unique environments.
Security Affairs
MAY 3, 2020
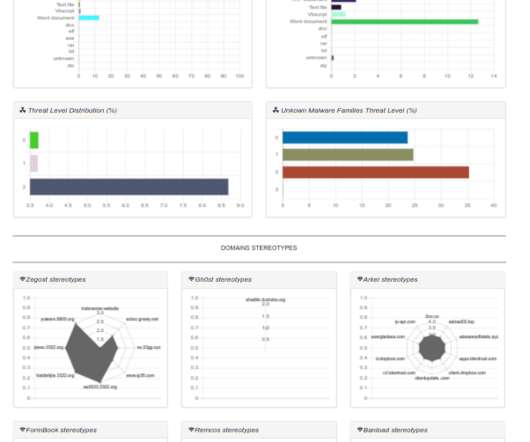
Today I am so happy to announce a big improvement in the cyber threats observatory (available for here ). Screenshot Cyber Threats Observatory ( HERE ). According to shared information, the Cyber Threats Observatory Dashboard is composed by the following sections: Malware Families Trends. What you find.

Penetration Testing
DECEMBER 12, 2023
On the 12th of December 2023, SAP Security Patch Day published 15 new Security Notes alongside updates to 2 previously released notes, fortifying SAP’s commitment to safeguarding its vast ecosystem against cyber threats.

The Last Watchdog
JANUARY 2, 2024
In today’s digital landscape, organizations face numerous challenges when it comes to mitigating cyber risks. Related: How AI is transforming DevOps The constant evolution of technology, increased connectivity, and sophisticated cyber threats pose significant challenges to organizations of all sizes and industries.

Penetration Testing
DECEMBER 21, 2023
In the shadowy realms of cyberspace, threats evolve as swiftly as the technologies they exploit. At the heart of... The post Beyond Breaches: 2024’s Cyber War – Extortion, Manipulation, and New Battlegrounds appeared first on Penetration Testing.

NetSpi Executives
FEBRUARY 13, 2024
Tim’s extensive background as a security analyst, pentester, director of Red Team , and chief technology officer for leading global companies brings a wealth of insights to the table. Therefore, the focus with proactive security lies in outpacing cyber threats.

IT Security Guru
DECEMBER 9, 2020
million fine handed to Marriott International for a cyber attack that took place between 2014 and 2018 and compromised the personal information (including emails addresses, phone numbers and passport details) of countless customers. Cyber threats are a real and significant problem. This however was small fry compared to the £18.4

The Last Watchdog
NOVEMBER 1, 2023
In the last year alone, advisers and wealth managers in financial sectors have witnessed an 80% increase in cyber threats and intrusion activity, with investment advisers being particularly vulnerable due to the sensitive nature of the data they handle. AdviserCyber doesn’t just ship cybersecurity software and call it a day.

NetSpi Executives
JANUARY 8, 2024
In case you missed it, Chubb, one of the leading publicly traded property and casualty insurance companies, announced an innovative collaboration with NetSPI to strengthen client cyber-risk profiles via enhanced attack surface management and penetration testing solutions.

Joseph Steinberg
JANUARY 18, 2024
Securing Success: The Crucial Role of a Cybersecurity Specialist in a Growing Business Human society is increasingly dependent on computer systems and the data housed and utilized within IT (information technology) infrastructure. Moreover, a cybersecurity specialist plays a crucial role in establishing robust security policies and protocols.
Appknox
MAY 23, 2024
In an era of digital innovation and technological advancements, robust application security has never been more crucial. As cyber threats continue to evolve, organizations must stay ahead of the curve to protect their sensitive data and maintain the security of their users.

NetSpi Executives
FEBRUARY 13, 2024
Tim’s extensive background as a security analyst, pentester, director of Red Team , and chief technology officer for leading global companies brings a wealth of insights to the table. Therefore, the focus with proactive security lies in outpacing cyber threats.

NetSpi Executives
FEBRUARY 13, 2024
Tim’s extensive background as a security analyst, pentester, director of Red Team , and chief technology officer for leading global companies brings a wealth of insights to the table. Therefore, the focus with proactive security lies in outpacing cyber threats.

IT Security Guru
JUNE 30, 2023
With cyber threats constantly dominating headlines, the draw of a career in cybersecurity has never been higher for young professionals. According to Glassdoor , the national average salary for a Cyber Security professional in the UK is around £43,711 per year. This exposure helps bridge the gap between theory and practice.

IT Security Guru
OCTOBER 2, 2023
The number of security technologies often results in fragmented data and hinders a comprehensive threat-hunting approach. Automated threat hunting has become a solution that can advance the capabilities of any security team. Security systems use advanced algorithms to streamline and enhance the threat hunting process.
NopSec
AUGUST 25, 2022
Lisa has a passion for connecting business with technology and thrives in transforming disruptive technology into leading solutions. In this episode, Jermaine Blyther, the Director of Threat and Vulnerability Management at OneMain Financial, discusses weaknesses in the Vulnerability Management field.

NetSpi Executives
MAY 24, 2024
With deep roots in penetration testing, plus consistent recognition for our people, process, and technology by global analyst firms (see: GigaOm ASM Radar Report ), NetSPI is uniquely positioned to help security teams take a proactive approach to security with more clarity, speed, and scale than ever before.

SecureWorld News
SEPTEMBER 3, 2023
From data breaches to sophisticated cyberattacks, enterprises are continuously at risk from a vast spectrum of potential cyber threats from malicious actors. The need of the hour is not just to react to these threats but to anticipate and mitigate them proactively.

Cytelligence
NOVEMBER 16, 2023
In today’s digital landscape, cyber threats pose a significant risk to organizations of all sizes. With the correct mix of strategies and frameworks, the playing field can level out and lean security teams can effectively defend against cyber threats. Data Defense Encrypt sensitive data both at rest and in transit.

NetSpi Executives
MAY 1, 2024
With deep roots in penetration testing, plus consistent recognition for our people, process, and technology by global analyst firms (see: GigaOm ASM Radar Report ), NetSPI is uniquely positioned to help security teams take a proactive approach to security with more clarity, speed, and scale than ever before.

Security Affairs
NOVEMBER 6, 2018
While developing the insurance program the two companies have scored more than 20 crypto exchanges and crypto wallets providers using both open-source information, available on exchanges’ websites and analytical capabilities of Group-IB’s Threat Intelligence (TI) system. Security Affairs – cyber insurance, cryptocurrency exchanges ).

IT Security Guru
JANUARY 26, 2024
In the current digital era, technology has become an integral part of various industries, and the transport industry is not left behind. Regular security assessment and penetration testing can also be carried out to identify potential vulnerabilities that, if exploited by cyber threats, may compromise the systems of vehicles.

SecureWorld News
MARCH 20, 2024
However, as the nature of cyber threats continues to evolve, so too do the offerings of cyber insurance, expanding to provide more comprehensive risk management solutions. The dynamic nature of cyber risks, evidenced by the rising frequency and costs of attacks, further complicates this issue.

Joseph Steinberg
JANUARY 19, 2024
Securing Success: The Crucial Role of a Cybersecurity Specialist in a Growing Business Human society is increasingly dependent on computer systems and the data housed and utilized within IT (information technology) infrastructure. Moreover, a cybersecurity specialist plays a crucial role in establishing robust security policies and protocols.

SecureWorld News
OCTOBER 22, 2023
Cyber challenges facing businesses expanding overseas Companies expanding into overseas markets face amplified cyber security challenges. Benefits of safeguarding global assets Properly securing critical assets and data against cyber threats when operating overseas provides major benefits.

SecureWorld News
FEBRUARY 17, 2024
Wearable technologies continuously monitor vital signs such as heart rate, while larger equipment like dialysis machines and ventilators operate tirelessly to support critical bodily functions. IoMT advances this technology by assisting healthcare providers in evaluating, treating, diagnosing, and monitoring patient health conditions.

The Last Watchdog
DECEMBER 26, 2018
Modern cyber threats often are not obvious – in fact it is common for them to lurk inside a business’ systems for a long time without anyone noticing. In an ideal world there would no dwell time at all, and threats would be identified before they can penetrate business’ defenses. SIEMs vs. UEBAs. Tapping professionals.

Cytelligence
DECEMBER 11, 2023
They leverage cutting-edge technologies and methodologies to analyze and mitigate risks, ensuring their clients are protected against present and future cyber threats. These include comprehensive security audits, penetration testing, incident response planning, and user awareness training.

Security Affairs
DECEMBER 2, 2022
Threat actors could exploit drones for payload delivery, kinetic operations, and even diversion, experts warn. Once a niche technology, drones are about to explode in terms of market growth and enterprise adoption. Dronesploit seeks to combine various tools useful for penetration testing specific to drone platforms.

eSecurity Planet
FEBRUARY 2, 2024
While Teslas aren’t the typical business IoT device, their connection to the internet makes them a cyber threat as much as your business’s other IoT technology. But the access technology can actually be exploited, allowing threat actors to reach the business’s IP network.

eSecurity Planet
JANUARY 12, 2021
Security risk assessments are one of the best measures your organization can take to protect the organization from cyber threats. As technology and business change, threats evolve and the internal or external landscape of your business fluctuates, so these routine audits play a pivotal role in keeping danger at bay.

eSecurity Planet
JUNE 15, 2023
Assign value In this phase, you assign a value to each asset based on its business importance and potential exposure to cyber threats. This involves assessing how likely it is that a vulnerability could be exploited by a cyber threat, as well as the potential impact of an exploit on your organization.
SC Magazine
MAY 17, 2021
5G is among the technologies that researchers predict will have a big impact on the security landscape in the next decade. “In fact, the overwhelming majority of the threats we envisage were present in some form, at least, by 2020.” Increased automation could change our understanding of insider threats, said Baines.

CyberSecurity Insiders
JANUARY 28, 2022
Because of the trend digital transformation, almost every company in every vertical has an information technology or operational technology component vital to successful operations. Technology disruption Technology disruption assists companies to evolve into new business models and upgrade their traditional modes of operating business.
Centraleyes
DECEMBER 11, 2023
A Quick Overview of the Five DORA Pillars The Digital Operational Resilience Act (DORA) establishes a transformative regulatory framework across five pillars to address Information and Communication Technology (ICT) risks in the EU financial sector.

SecureWorld News
JUNE 12, 2023
Certified professionals often earn 20% more than their counterparts who have not completed the relevant tests and exams. Stay on top of industry changes The cybersecurity sector is in a state of constant change, with new technologies and methodologies introduced on a regular basis. based on reviews on Coursera) Cost: Free [link] 2.

eSecurity Planet
JUNE 21, 2022
CISA is ISACA’s (Information Systems Audit and Control Association) high-level certification designed for those who audit, control, monitor, and assess an organization’s information technology and business systems. The 4-5 hour exam includes up to 180 questions. Training is available in a variety of formats.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content