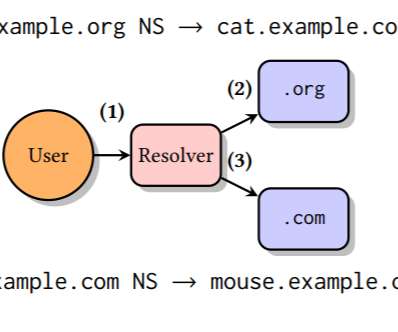
Joint Advisory Warns of Fast Flux DNS Tactics Evading Detection
SecureWorld News
APRIL 8, 2025
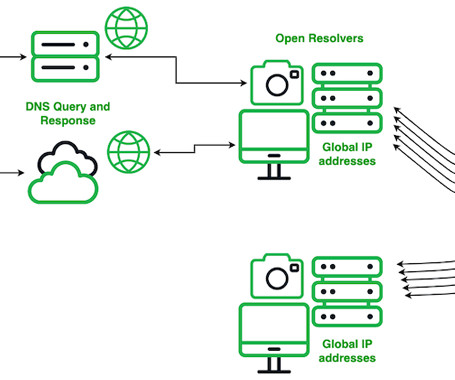
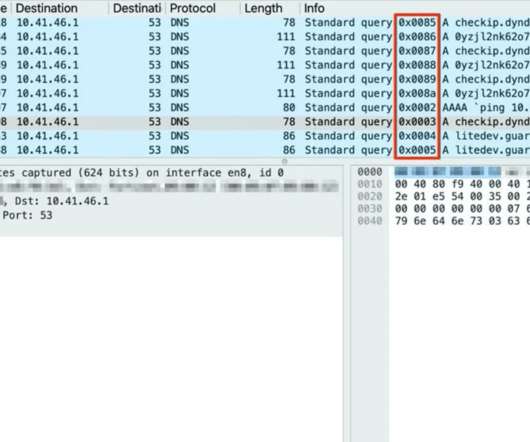
A joint cybersecurity advisory was recently issued by the United States National Security Agency (NSA), Cybersecurity and Infrastructure Security Agency (CISA), Federal Bureau of Investigation (FBI), and their counterparts from Australia, Canada, and New Zealand. Fast flux DNS is not new.










































Let's personalize your content